
Key Takeaways
- Use this 21-point heuristic framework, which combines Nielsen’s 10 usability principles, CRO tactics, and cybersecurity UX elements, to audit SaaS websites in under 2 hours.
- ESET’s main UX issues include a 7-field download form, trust signals hidden below the fold, and unclear AI value propositions, resulting in a 65% overall score.
- Prioritize quick wins such as moving trust logos above the fold, standardizing CTA buttons, and simplifying forms to drive 15-25% conversion rate lifts.
- Apply a 1-5 severity scoring system to rank fixes by business impact, with special focus on mobile experience and trust architecture for cybersecurity SaaS.
- Partner with SaaSHero for a discovery call to implement this framework and grow ARR for your cybersecurity SaaS.

Tools, Setup, and ESET Context
Run this evaluation with browser developer tools, screenshot software, and a scoring sheet that uses a 1-5 severity scale. A score of 1 covers cosmetic issues, while 5 flags critical conversion blockers. Severity assessment rates issues from minor annoyances to critical blockers so you can prioritize work effectively.
Reviewers should understand Nielsen’s usability principles before starting. ESET’s 2026 context includes global cybersecurity leadership, a mobile-first redesign, and AI threat detection pages. Plan 1-2 hours for a full evaluation and reduce bias by using three independent reviewers.
Four-Step Heuristic Framework for Cybersecurity SaaS
This tutorial uses a simple four-step process. First, select 21 heuristics across three categories. Second, audit ESET pages in a consistent order. Third, score severity using shared criteria. Fourth, prioritize fixes based on impact and effort.
The framework blends Nielsen usability principles, CRO best practices, and security-specific UX checks for a complete view of performance.
| Group | Heuristic | Description |
|---|---|---|
| Nielsen 10 | 1. Visibility of System Status | Timely feedback during page interactions |
| Nielsen 10 | 2. Match System/Real World | Familiar language and concepts |
| Nielsen 10 | 3. User Control and Freedom | Undo/redo options available |
| Nielsen 10 | 4. Consistency and Standards | Uniform design patterns |
| Nielsen 10 | 5. Error Prevention | Design prevents user errors |
| Nielsen 10 | 6. Recognition vs Recall | Information visible, not memorized |
| Nielsen 10 | 7. Flexibility and Efficiency | Shortcuts for expert users |
| Nielsen 10 | 8. Aesthetic Minimalist Design | Relevant information only |
| Nielsen 10 | 9. Error Recognition/Recovery | Clear error messages |
| Nielsen 10 | 10. Help and Documentation | Easy-to-find assistance |
| CRO | 11. Relevance | Ad-to-page message match |
| CRO | 12. Clarity | 5-second value proposition test |
| CRO | 13. Trust | Visible credibility indicators |
| CRO | 14. Friction | Minimal form fields and steps |
| CRO | 15. Social Proof | Customer logos and testimonials |
| CRO | 16. Urgency | Clear call-to-action hierarchy |
| CRO | 17. Mobile Optimization | Responsive design quality |
| Security | 18. Privacy Cues | Visible policy links |
| Security | 19. Threat Communication | Clear security messaging |
| Security | 20. Compliance Indicators | Certification badges |
| Security | 21. Authenticity Signals | Legitimate business markers |
Applying the 21 Heuristics to ESET
Nielsen’s 10 Heuristics on ESET’s Core Pages
Start with Nielsen’s foundational 10 usability heuristics developed in 1994. Focus on ESET’s homepage, downloads page, and pricing pages to cover the full journey from awareness to trial.
| Principle | ESET Check | Finding | Score (1-5) |
|---|---|---|---|
| Visibility of System Status | Homepage loading indicators | No progress feedback during page transitions | 3 |
| Match System/Real World | Navigation terminology | Some specialized terms in navigation | 1 |
| User Control and Freedom | Download process | No clear back button in multi-step flow | 4 |
| Consistency and Standards | Button styling | Inconsistent CTA button colors across pages | 2 |
Screenshot analysis shows that ESET’s homepage hero section lacks strong trust indicators above the fold. The download page uses a 7-field form, which creates unnecessary friction for new users. Navigation labels are mostly clear, although some industry-specific terms may slow first-time visitors.
CRO Principles on Messaging, Trust, and Forms
Next, apply conversion-focused heuristics that support revenue growth. The 5-second value proposition test shows that ESET’s AI capabilities do not stand out clearly in the hero copy. Trust signals such as customer logos appear below the fold, which delays credibility building.
| CRO Principle | ESET Assessment | Impact | Score (1-5) |
|---|---|---|---|
| Relevance | Ad-to-landing page match | Generic messaging lacks specificity | 3 |
| Clarity | Value proposition clarity | AI benefits not immediately clear | 4 |
| Trust | Above-fold credibility | Customer logos positioned too low | 4 |
| Friction | Download form complexity | 7 fields increase abandonment risk | 5 |
Pricing pages often miss clear feature comparisons, which makes plan selection harder. Book a discovery call to review your own cybersecurity SaaS against these same CRO checks.
Cybersecurity UX Heuristics for Trust and Compliance
Security-specific UX elements strongly influence trust for cybersecurity SaaS buyers. NIST IR 8596 emphasizes advanced threat detection and response practices, which your interface should communicate clearly.
| Security Heuristic | ESET Evaluation | Trust Impact | Score (1-5) |
|---|---|---|---|
| Privacy Cues | Policy link visibility | Privacy policy buried in footer | 3 |
| Threat Communication | Security messaging clarity | Some specialized terminology used | 2 |
| Compliance Indicators | Certification badges | Limited compliance visibility | 4 |
| Authenticity Signals | Business legitimacy markers | Contact information not prominent | 2 |
ESET Audit Results and Severity Scoring
The full evaluation highlights several conversion barriers across ESET’s main pages. 86% of major cyber incidents result in operational downtime and reputational damage, so a smooth UX directly supports perceived reliability.
| Finding | Page | Severity (1-5) | SaaS Impact |
|---|---|---|---|
| Download form: 7 fields | Downloads | 5 (High) | +20% abandonment risk |
| Trust logos below fold | Homepage | 4 (High) | Reduced credibility signals |
| Unclear AI value prop | Homepage | 4 (High) | Missed differentiation |
| Inconsistent CTA styling | All pages | 3 (Medium) | Conversion confusion |
| Mobile navigation density | All pages | 3 (Medium) | Mobile user experience |
| Privacy policy buried | All pages | 3 (Medium) | Trust barrier |
| Specialized terminology | Navigation | 2 (Low) | Minor comprehension issues |
| No progress indicators | Multi-step flows | 2 (Low) | User uncertainty |
The total audit score reaches 68 out of 105, or 65%. This result signals strong opportunities to improve form friction, trust signal placement, and mobile experience.
Prioritized UX Improvements and SaaSHero Recommendations
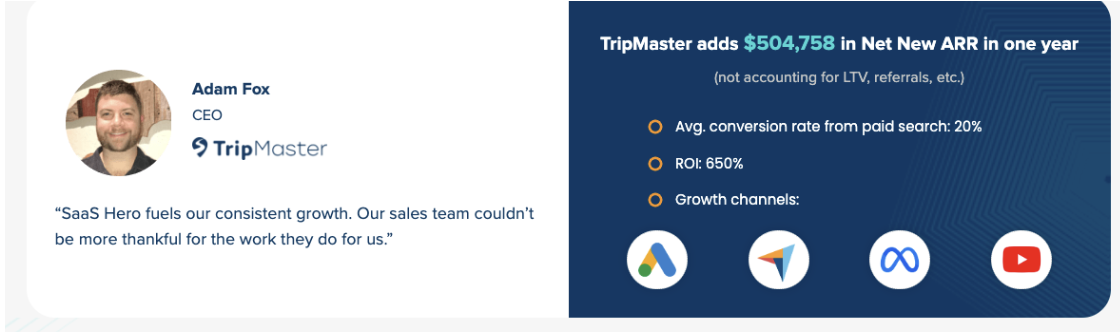
The roadmap starts with high-impact, low-effort changes before moving to deeper UX work. This approach mirrors the process that delivered $504k ARR growth for TripMaster through structured CRO work.
| Priority | Fixes | Effort (Days) |
|---|---|---|
| Quick Wins | Move trust logos above fold | 1 |
| Quick Wins | Standardize CTA button styling | 1 |
| Quick Wins | Simplify navigation terminology | 2 |
| Medium | Reduce download form fields | 3 |
| Medium | Clarify AI value proposition | 5 |
| Strategic | Mobile navigation redesign | 10 |
| Strategic | Comprehensive trust architecture | 15 |
CRO audits and implementation start at $1,250 per month with month-to-month flexibility. Cybersecurity SaaS expertise keeps messaging technically accurate while still focused on conversion. Book a discovery call to review your heuristic evaluation and build a practical roadmap.
Measurement and Validation Plan
Track pre and post changes using conversion rate, form completion rate, and mobile engagement metrics. SaaSHero supports GA4 and CRM integration so you can attribute revenue and prove ROI. Most clients see 15-25% conversion rate lifts after they implement a full heuristic evaluation plan.
FAQ
How should I score heuristic violations?
Use a 1-5 severity scale where 1 represents cosmetic issues with minimal impact. Scores of 2 or 3 indicate usability problems that affect some users. A score of 4 represents major issues that affect most users. A score of 5 flags critical blockers that prevent task completion.
Consider both how often the issue appears and how strongly it affects business outcomes when you assign scores.
Can this framework be adapted for other cybersecurity SaaS websites?
The 21-point framework works across cybersecurity SaaS platforms with minor adjustments. Adapt the security-specific heuristics to match your focus area, such as endpoint protection, network security, or compliance. Keep the core Nielsen principles and CRO fundamentals consistent.
The scoring methodology remains the same, which makes results comparable across products and teams.
What timeline should I expect for implementing heuristic evaluation fixes?
Quick wins usually take 1-3 days to implement. Medium-priority fixes often require 3-7 days. Strategic improvements such as navigation redesign or trust architecture can take 2-4 weeks.
The initial audit typically finishes within one week and includes ongoing optimization support with monthly progress reviews.
How much does professional heuristic evaluation cost?
Comprehensive UX audits start at $1,250 per month and include heuristic evaluation, competitor analysis, and an implementation roadmap. Landing page optimization is available for $750 per page. This investment often produces 15-25% conversion rate improvements within about 60 days.
What results can I expect from systematic heuristic evaluation?
Clients usually see 15-25% conversion rate lifts, lower bounce rates, and higher form completion rates. SaaSHero has delivered $504k in net new ARR growth and helped clients reach 80-day payback periods through structured UX improvements.
Actual results depend on your current performance and how thoroughly your team implements the recommendations.
Should I prioritize mobile optimization in my heuristic evaluation?
Mobile optimization deserves high priority for cybersecurity SaaS. Mobile traffic often represents 40-60% of B2B SaaS visits, and mobile conversion gaps can hide major revenue losses.
Focus on touch target sizing, simplified navigation, and short, focused forms for smaller screens. Mobile improvements frequently deliver the strongest ROI in heuristic evaluation projects.

