Key Takeaways
-
Cybersecurity buyers researching competitor pricing and alternatives bring high-intent traffic for Net New ARR, even with CPCs from $10 to $97.
-
Use this 5-step framework: intent research, compliant creatives, campaign setup with negatives, CRO, and revenue-focused scaling.
-
Target pricing, complaint, and review intent buckets with message-matched landing pages that use factual comparisons and visible trust signals.
-
Run Target ROAS bidding with CRM imports to cut CAC by 20–30% and aim for payback periods under 80 days while tracking pipeline to closed-won.
-
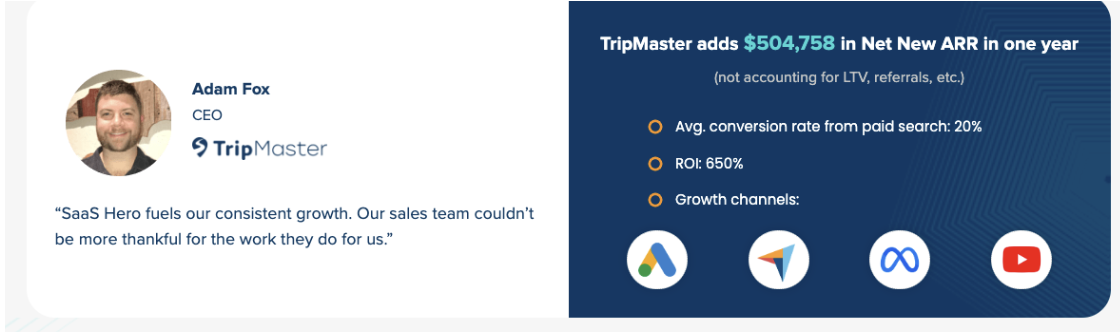
Apply this playbook to pursue results like $504k in new ARR and 650% ROI, then see how SaaSHero can replicate these outcomes for your cybersecurity brand.
Prerequisites and Context for Cybersecurity Conquesting
Effective competitor conquesting in cybersecurity starts with the right stack and guardrails. You need Google Ads and LinkedIn Ads access, CRM integration with HubSpot or Salesforce, baseline performance data including CAC and LTV, and legal review of comparative advertising guidelines. The 2026 landscape brings higher risk and cost, with CPCs for cybersecurity-related keywords ranging from $10 to over $97 and more aggressive competitor retaliation.
Modern AI-powered ad platforms now rely on Target ROAS bidding with CRM imports so campaigns optimize for pipeline value instead of raw form fills. Real-time bidding adjustments now occur within milliseconds, which makes clean, complete CRM data a non-negotiable for performance.
Plan for 2–4 weeks of initial setup and payback periods around 80 days when campaigns follow this structure. Keep your primary focus on revenue and Net New ARR instead of vanity metrics like impressions or clicks.
Process Overview: The 5-Step Conquesting Framework
The conquesting framework follows five sequential steps: intent keyword research, compliant creative development, campaign setup with negative keyword hygiene, conversion rate optimization, and revenue tracking with scale optimization.
These three intent buckets reflect distinct buyer mindsets that call for different messaging and offers:
|
Intent Bucket |
Keywords |
User Psychology |
|---|---|---|
|
Pricing |
“[Competitor] pricing/cost” |
Price-sensitive renewals |
|
Complaint |
“[Competitor] down/support issues” |
Frustrated churn risks |
|
Review |
“[Competitor] reviews/alternatives” |
Validation-seeking |
Each intent bucket needs tailored landing page messaging and ad copy that match expectations and reduce friction so more visitors convert.
Step-by-Step Instructions
Step 1: Intent Research for Competitor Keywords
Start with Google Keyword Planner and Ahrefs to find 50–100 competitor-related keywords across pricing, complaint, and review intent buckets. Prioritize cybersecurity-specific phrases such as “Palo Alto alternatives cybersecurity” and “CrowdStrike pricing enterprise” instead of broad brand searches that lack buying context.
Remove navigational queries like “[competitor] login” or “[competitor] support portal” so you avoid paying for existing customers seeking help. Allocate meaningful budget to competitor campaigns because they usually deliver stronger lead quality and higher downstream revenue.
Step 2: Compliant Creatives and Comparison Landing Pages
Build comparison landing pages that speak directly to the search intent while staying within legal boundaries. Use factual feature comparisons, avoid competitor logos, and skip sensational or confusing headlines that could invite legal review.
For example, a comparison focused on deployment time and total cost of ownership can address speed and budget concerns for security teams:
|
Feature |
CrowdStrike |
Your SaaS |
|---|---|---|
|
Deployment Time |
90 days |
30 days |
|
Annual TCO |
$200,000 |
$150,000 |
Place trust signals such as G2 badges, analyst quotes, and customer testimonials above the fold so visitors see proof early. For complaint-intent keywords like “Norton support issues,” create problem–solution pages that name the pain clearly and position your platform as the safer, more responsive alternative.
Step 3: Campaign Setup and Bidding Strategy
Set up Target ROAS bidding with CRM offline conversion imports so Google optimizes toward pipeline value instead of simple form completions. Feeding MQL, SQL, and closed-won data into the platform often cuts CAC by 20–30% because the algorithm learns which clicks create revenue.
Add comprehensive negative keywords such as “[competitor] login,” “[competitor] careers,” and “[competitor] stock price” to filter out non-buyers and protect budget. After you block irrelevant traffic, use exact and phrase match keywords for control, then test broad match only when paired with strong negative lists.
Layer LinkedIn ABM campaigns for accounts that justify personalized outreach beyond search. Target job titles like CISO and IT Director at companies showing intent signals through Bombora or similar tools so your ads reach real decision-makers.
Step 4: Conversion Rate Optimization for Conquest Pages
Design landing pages so visitors grasp your value proposition and next step within five seconds of arrival. Keep message match tight between ad copy and landing page headlines so users feel they landed in the right place.
Write clear, benefit-driven headlines and place prominent demo or trial CTAs that spell out the action you want. Support those headlines with specific, concrete claims instead of vague promises, because statements like “30-day deployment” usually convert better than “fast implementation.” Then reinforce credibility with social proof such as customer logos and security certifications that reduce perceived switching risk.
Struggling with high CPCs and low conversion rates? SaaSHero’s cybersecurity expertise has helped clients cut CPL by 10x, and you can explore how we would approach your specific challenges.
Step 5: Launch, Monitor, and Scale
Review campaigns weekly and aim for impression share above 20% on priority keywords while you refine bids. Rely on CRM and pipeline data when you adjust budgets and bids, because platform-reported metrics alone rarely show true revenue impact. Cybersecurity sales cycles often last 6–9 months, so you need patience and longer attribution windows to judge performance accurately.
Test new ad variations on a regular cadence, with special focus on headlines that challenge incumbent vendors or highlight switching benefits such as faster deployment or lower TCO. Scale winning campaigns gradually while you watch CAC, payback, and ROAS so growth does not erode efficiency.
Measurement and Validation for Cybersecurity Conquesting
Connect ad clicks to revenue by implementing GCLID-to-CRM tracking across your forms and pipelines. Use 365-day attribution windows to reflect cybersecurity’s long buying cycles and to capture a more accurate view of ROAS.
These benchmarks provide practical targets and tie back to the earlier payback expectations:
|
Metric |
Target |
|---|---|
|
Cost Per Lead |
<$200 |
|
Payback Period |
<80 days (based on our client benchmark) |
|
ROAS |
Profitable and improving quarter over quarter |
Track pipeline movement from MQL to SQL to closed-won and assign values to each stage so bidding algorithms can prioritize higher-quality opportunities. Keep your primary lens on Net New ARR instead of total pipeline so you measure true incremental growth.
Need help setting up proper attribution and tracking? Request a free audit of your current measurement setup.
Advanced Conquesting Variations for Cybersecurity SaaS
Extend conquesting beyond search into review platforms like G2 and Capterra, where buyers actively compare alternatives and shortlist vendors. ABM programs that target specific accounts can lift win rates when you pair them with intent data and tailored messaging across channels.
Stay ahead of emerging AI-driven threats and categories by testing terms like “zero-trust alternatives” and “SASE solutions” as they gain traction. AI-driven multivariate testing now evaluates dozens of creative variations at once, which improves performance without constant manual tweaks.
For large enterprise deals, add account-based advertising on LinkedIn that targets named companies and specific decision-makers surfaced by your intent monitoring platforms.
Summary and Next Steps for Your Conquesting Program
Begin with one focused competitor campaign targeting high-intent keywords, connect every lead to your CRM, and scale based on Net New ARR results. Keep message match tight, maintain strong negative keyword hygiene, and use long-term attribution so you protect ROI as you grow.
Work with cybersecurity marketing specialists who understand complex buying committees, compliance needs, and long sales cycles. SaaSHero’s systematic conquesting strategies have helped clients achieve outcomes such as $70M Series A raises and 650% ROI, and the same approach can guide your next stage of growth.
Frequently Asked Questions
What are the legal risks of competitor conquesting in cybersecurity ads?
Competitor conquesting stays on safe legal ground when you follow clear rules. Use competitor names only in factual comparisons, avoid their logos or trademarks in ad creative, and write headlines that clearly identify your company as the advertiser. Stick to truthful feature comparisons and avoid misleading claims about competitor products or services. Most legal disputes stem from trademark misuse or false advertising, both of which you can prevent with careful, compliant creative development.
What are typical CPC benchmarks for cybersecurity competitor campaigns?
Cybersecurity competitor keywords can range from $10 to over $97 per click, and enterprise-focused terms usually sit at the higher end. The stronger intent of users searching for competitor alternatives often delivers better conversion rates and lower cost per qualified lead than generic cybersecurity terms. Plan to allocate 15–20% of total ad spend to competitor campaigns while you monitor efficiency metrics closely.
How does SaaSHero’s pricing work for cybersecurity conquesting campaigns?
SaaSHero offers transparent monthly retainers starting at $1,250 for dedicated campaign management, with no percentage-of-spend fees or long-term contracts. This flat-fee structure keeps recommendations aligned with performance data instead of agency revenue incentives. Pricing scales with ad spend and channel count so finance teams get predictable costs while marketing teams gain room to grow.
How long does it take to see results from cybersecurity conquesting campaigns?
Initial campaign setup usually takes 2–4 weeks for keyword research, landing page builds, and tracking implementation. Given the extended sales cycles discussed earlier, you can often see meaningful pipeline impact within the first few months, with closed revenue following 6–9 months later. During the early phase, track leading indicators such as MQL volume, cost per lead, and opportunity creation while you build toward long-term revenue goals.
What makes cybersecurity conquesting different from other B2B SaaS verticals?
Cybersecurity conquesting demands deeper technical fluency and longer attribution windows because buying decisions involve security, legal, and compliance stakeholders. Buyers act more cautiously and expect extensive social proof, documentation, and risk mitigation. High average contract values justify premium CPCs, but campaigns must focus on pipeline quality and unit economics instead of raw lead volume to stay profitable.
Ready to master competitor conquesting for your cybersecurity SaaS? Let’s map out your specific conquesting strategy and competitive landscape.

