
Key Takeaways
- Signature-based detection reaches 99% accuracy for known threats but fails completely against zero-day and polymorphic malware.
- Heuristic analysis detects 70-90% of zero-day threats through behavioral patterns but suffers 5-22% false positive rates.
- Hybrid systems that combine both methods reach 95-97% efficacy, detect threats 60% faster, and save $2.2M per breach.
- Real-world incidents like WannaCry and GTG-1002 AI swarms show how pure signature-based tools struggle against adaptive threats.
- Cybersecurity SaaS companies can apply similar heuristic principles to marketing; book a discovery call with SaaSHero to turn competitor evaluation traffic into conversions.
How Signature-Based Detection Works in Practice
Signature-based detection acts as a reactive security layer that spots malware through pattern matching against a database of known threat signatures. This approach scans files, network traffic, and system behaviors against stored hash values, byte sequences, and behavioral fingerprints from previously identified malicious code. The system flags any matches as potential threats, which delivers strong protection against known malware variants. The same design creates a hard limit against new attack vectors that do not yet exist in the signature database.
How Heuristic and ML-Based Detection Finds New Threats
Heuristic analysis uses a proactive model that focuses on suspicious behaviors, code structures, and system interactions that deviate from normal patterns. Instead of relying on exact matches, heuristic engines evaluate unusual API calls, encryption activity, file modification patterns, and network communication behaviors. Machine learning models in 2026 achieve above 97% accuracy in phishing detection by combining domain reputation checks, message structure analysis, and behavioral pattern recognition. The result is earlier detection of novel and fast-changing threats.
Why Hybrid Detection Became the Default
The shift toward hybrid approaches shows that the industry accepts a simple reality. Neither signatures nor heuristics alone can provide complete protection. Organizations using AI-powered security detect threats 60% faster and save $2.2 million per breach. These outcomes come from pairing traditional signature matching with advanced behavioral analysis in a single layered system.
Heuristic vs Signature-Based: Side-by-Side Comparison
| Detection Aspect | Signature-Based | Heuristic Analysis | 2026 Winner |
|---|---|---|---|
| Zero-Day Detection | 0% effectiveness | 70-90% detection rate | Heuristic |
| Known Threat Detection | 99% accuracy | 85-95% accuracy | Signature |
| False Positive Rate | 1-3% | 5-22% depending on tuning | Signature |
| Resource Consumption | Low CPU/Memory | High processing overhead | Signature |
| Update Requirements | Constant signature updates | Periodic rule refinement | Heuristic |
Strengths and Limits of Signature-Based Detection
Signature-based detection fits enterprise environments that need predictable, low-maintenance security controls. This method delivers high accuracy against known threats, low system resource usage, and straightforward rollout across complex infrastructure. However, signature-based detection fails against unknown or polymorphic threats that rely on code obfuscation, encryption, or dynamic generation techniques.
| Signature-Based Detection | Pros | Cons |
|---|---|---|
| Performance | Fast scanning, low resource usage | Ineffective against zero-day attacks |
| Accuracy | 99% detection of known threats | Vulnerable to polymorphic malware |
| Maintenance | Automated signature updates | Constant database maintenance required |
Why Heuristic Analysis Still Misses the Mark
Heuristic detection struggles with false positives, especially inside large and complex enterprise environments. Microsoft’s AV Transparency Report Q1 2026 shows that 22% of legitimate .NET applications trigger false positives in heuristic engines, which creates operational noise and user frustration. In the same report, heuristic malware detection causes false positives in 18% of legitimate software, which highlights the tuning challenge for security teams.
Advanced attackers now design evasion techniques that specifically target heuristic systems. They mimic legitimate application behaviors, slowly stage malicious payloads, and use machine learning to adapt attack patterns over time. These tactics keep the arms race active between detection vendors and threat actors.
SaaSHero applies similar heuristic thinking to conversion rate improvement. Our team identifies behavioral patterns that signal purchase intent while reducing false positives that could push away qualified buyers. Book a discovery call to see how our heuristic audits have lifted ROI for B2B SaaS platforms.
Real-World Attacks That Exposed Detection Gaps
Signature-based detection still works well for compliance-focused enterprises that mainly face known threats. Financial institutions that process standardized transactions and healthcare organizations that protect regulated patient data both benefit from this stability. The WannaCry ransomware outbreak showed both the strength and the weakness of this model. Organizations with current signature databases blocked the attack, while those with outdated definitions suffered broad infections.
Heuristic analysis shines against advanced tools like Cobalt Strike beacons, which use dynamic command-and-control patterns that slip past simple signature checks. SentinelOne’s AI-powered system achieves zero dwell time, compared to the industry average of 280 days for breach containment. This contrast shows how behavioral detection changes outcomes in real enterprise environments.
The November 2025 GTG-1002 AI swarm campaign exposed the limits of pure signature-based detection against coordinated, adaptive threats. This attack coordinated across 30 organizations with 80-90% autonomy, bypassing traditional monitoring while AI-powered anomaly detection identified the threat. Hybrid and AI-first systems handled this scenario more effectively.
Tool Benchmarks and Hybrid Detection Performance
| EDR/AV Solution | Signature Strength | Heuristic/ML Capability | 2026 Overall Efficacy |
|---|---|---|---|
| Kaspersky Security | Excellent (99% known threats) | Advanced behavioral analysis | 95% hybrid effectiveness |
| SentinelOne Singularity | Good (95% known threats) | Industry-leading AI/ML | 97% hybrid effectiveness |
| ClamAV Open Source | Good (90% known threats) | Basic heuristic rules | Limited effectiveness against zero-days |
Hybrid detection systems that combine signature matching with machine learning consistently outperform single-method tools. Organizations detect threats 60% faster and save $2.2 million per breach when they adopt AI-powered hybrid detection. Behavioral analysis layered on top of signature databases creates coverage for both known and unknown threat vectors.
Cybersecurity SaaS vendors that want to capture buyers who evaluate these enterprise tools need focused competitor conquesting strategies. Targeting high-intent search queries around detection technologies helps intercept evaluation traffic and convert prospects who compare solutions side by side.
SaaSHero Recommendation for Cybersecurity SaaS Growth
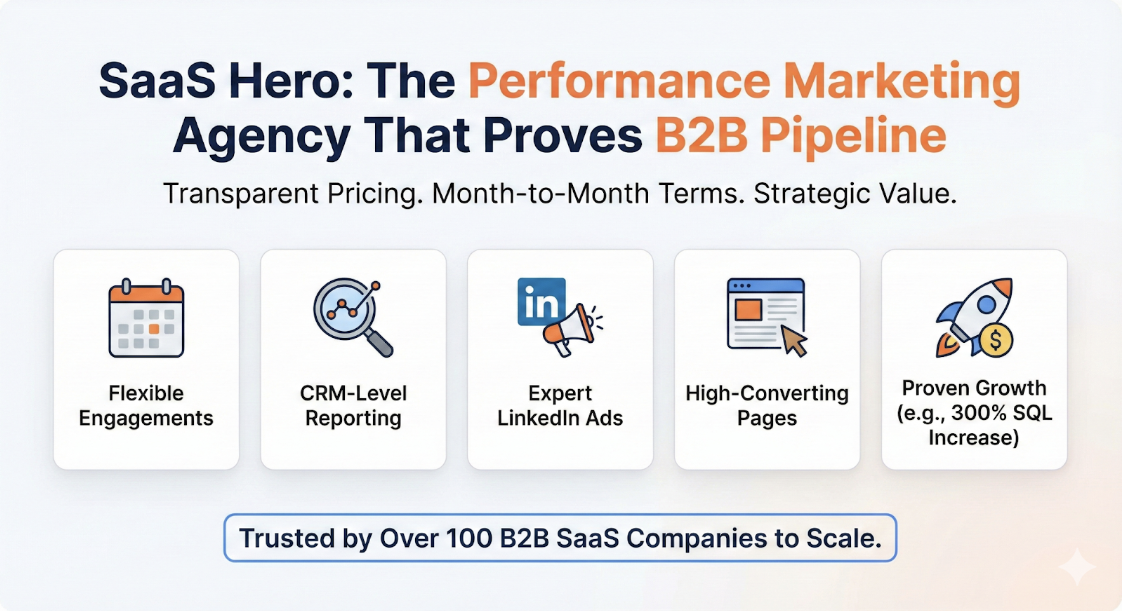
Hybrid detection systems outperform single-method approaches in security, and SaaSHero follows the same logic for marketing. Our team blends heuristic conversion analysis with targeted competitor conquesting to drive predictable cybersecurity SaaS growth. This approach has generated $504k in Net New ARR for B2B SaaS clients while keeping payback periods efficient.
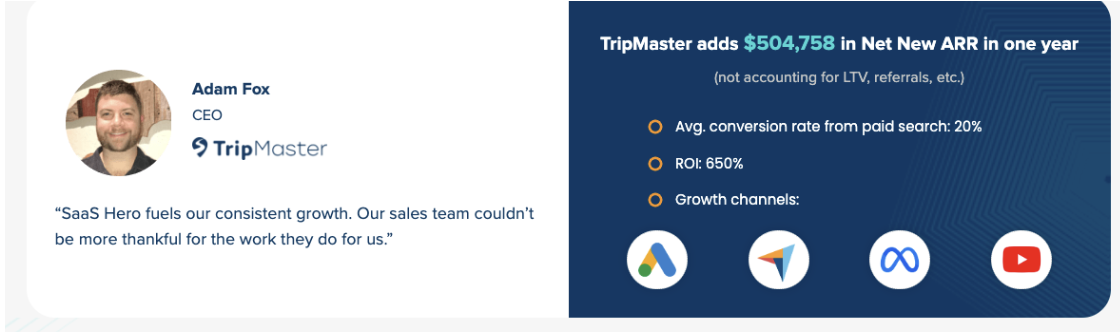
At $1,250 per month on a month-to-month agreement, SaaSHero offers the agility and performance focus that cybersecurity companies need to win market share in a fast-moving category.

Future Direction and a Simple Decision Framework
The cybersecurity market continues to move toward AI-enhanced hybrid detection that pairs the reliability of signatures with the flexibility of machine learning. Security leaders evaluating detection strategies should weigh zero-day exposure, tolerance for false positives, regulatory pressure, and available security staff. Most modern programs land on layered defenses that blend both methods instead of relying on a single technique.
Frequently Asked Questions
What is the main difference between signature-based and heuristic detection?
Signature-based detection identifies malware by matching files against a database of known threat signatures. Heuristic detection analyzes suspicious behaviors and code patterns to flag potentially malicious activity. Signature-based methods excel at detecting known threats with high accuracy. Heuristic analysis finds previously unknown malware variants through behavioral analysis.
What is the main drawback of signature-based IDS systems?
The primary limitation of signature-based intrusion detection systems is their inability to detect zero-day attacks or new malware variants that do not match existing signatures. These systems need constant updates to stay effective and cannot spot threats that use new attack vectors or polymorphic techniques that change their signatures.
Why is heuristic analysis not 100% reliable?
Heuristic analysis generates false positives because it relies on behavioral patterns and rule-based logic that can misread legitimate software activity as malicious. Complex enterprise environments with many different applications increase the chance of triggering heuristic rules. Skilled attackers can also design malware that mimics normal behavior to slip past detection.
What are the key advantages of heuristic detection methods?
Heuristic detection provides proactive protection against unknown threats, including zero-day exploits and polymorphic malware that signature-based systems miss. This method can detect malicious behavior patterns in real time without prior knowledge of specific threat signatures. That capability makes it valuable against advanced persistent threats and fast-evolving attack techniques.
How do signature-based and behavior-based detection methods compare?
Signature-based detection delivers higher accuracy for known threats with fewer false positives. Behavior-based detection offers broader coverage against unknown threats but creates higher false positive rates and greater resource usage. Modern enterprise security programs usually combine both methods to balance coverage and operational efficiency.
Conclusion
The choice between signature-based and heuristic malware detection depends on risk tolerance, threat exposure, and operational constraints. Hybrid approaches that combine both methods provide the broadest protection in the complex 2026 threat landscape. Cybersecurity SaaS companies that want to benefit from this demand need marketing programs that capture prospects while they evaluate detection technologies.
Book a discovery call with SaaSHero to turn your detection technology expertise into measurable ARR growth through our proven heuristic marketing methodology.

