
Key Takeaways for Cybersecurity Google Ads
- B2B cybersecurity Google campaigns can reach 3x ROAS by focusing on high-intent competitor conquesting keywords instead of broad category terms.
- Pricing, problem, and validation intent searches perform best when they connect to tailored landing pages with TCO comparisons and case studies.
- CRM integration enables accurate Net New ARR attribution and supports decisions based on CPQL, SQL volume, and pipeline velocity.
- Budget allocation typically scales from $5k per month for startups targeting 3x ROAS to $50k+ for enterprises aiming for 5.5x with flat-fee management.
- Avoid vanity metrics and percentage-of-spend agencies, and talk to our team about launching campaigns that prioritize pipeline over impressions.
Executive Summary and Revenue-Focused Framework
Successful B2B cybersecurity Google campaigns use a full-funnel approach that combines Search, Performance Max, and ABM tactics. This framework prioritizes high-intent keywords, competitor conquesting, and rigorous CRM tracking to achieve efficient CPQL and healthy payback periods.
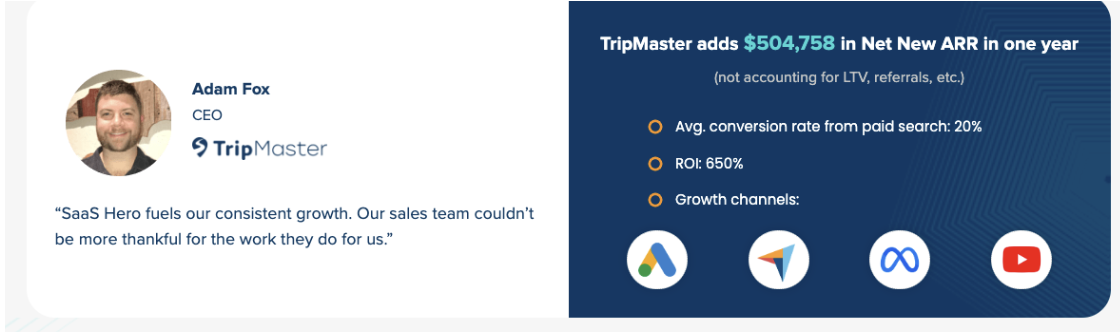
Key performance metrics work together to show both efficiency and revenue impact. Cost Per Qualified Lead (CPQL) measures how efficiently you acquire qualified leads from paid campaigns. Net New ARR attribution through CRM integration then connects those leads to closed revenue, proving whether campaigns actually drive growth. These revenue numbers feed into ROAS calculations, which show how much revenue you generate for every dollar spent. MQL to SQL conversion rates finally reveal whether your targeting attracts real buyers or fills the funnel with unqualified contacts.
The SaaSHero methodology follows four phases. First, the team audits existing performance to understand current gaps. Second, they implement competitor conquesting to capture high-intent demand. Third, they improve conversion rates across key landing pages. Finally, they scale profitable campaigns in a controlled and systematic way. The foundation of this approach starts with understanding your buyer landscape and selecting keywords that match their research behavior, which is where many cybersecurity campaigns fall short.
B2B Cybersecurity Buyer Behavior and Keyword Strategy
Cybersecurity buyers typically include CISOs, IT Directors, and security analysts across finance and healthcare verticals. These decision-makers research solutions through platforms like HubSpot and Salesforce marketplaces, analyst content, and peer networks before they engage vendors directly. Their research behavior creates specific search patterns, and high-intent keywords such as “alternative to Splunk” and “SIEM software” often produce qualified leads.
The 2026 keyword landscape favors intent quality over raw volume. Terms like “best PAM solution for healthcare” usually deliver stronger conversion rates than broad category terms with higher search volume but weaker buying intent. The table below shows how different keyword categories align with buyer intent and expected costs so you can prioritize spend on the queries most likely to create pipeline.
| Keyword Category | Example Terms | Est. CPC (2026) | Intent Level |
|---|---|---|---|
| Competitor Alternatives | CrowdStrike alternatives | Varies | High |
| Category + Pricing | EDR pricing, SIEM cost | Varies | High |
| Solution Specific | Ransomware protection, DLP software | Varies | Medium |
| Compliance Terms | SOC 2 security tools, HIPAA compliance | Varies | Medium |
Negative keyword hygiene plays a critical role in budget efficiency. You should exclude pure brand terms where users clearly seek login pages or support portals. At the same time, you should target modified searches that signal evaluation intent, such as “reviews,” “alternatives,” or “pricing.”
Key Tactics for Conquesting, Ad Copy, and Performance Max
Competitor conquesting often becomes the backbone of profitable cybersecurity campaigns. Bottom-of-funnel competitor keywords usually convert at a higher rate than top-of-funnel terms, which justifies higher CPCs for this more qualified traffic.
The conquesting framework focuses on three psychological intent buckets that match how buyers search when they evaluate alternatives.
Pricing Intent: Users who search “[Competitor] pricing” or “how much does [Competitor] cost” want clear cost comparisons. They respond best to dedicated comparison pages with transparent TCO breakdowns. These pages should highlight pricing tables, contract terms, and value gaps between your offer and the incumbent.
Problem Intent: Searches such as “[Competitor] alternatives” or “cancel [Competitor]” signal frustration with current tools. These visitors need problem-solution pages that address known competitor weaknesses and show how your product fixes those issues. Switching case studies and migration stories help reduce perceived risk.
Validation Intent: Terms like “[Competitor] reviews” or “[Competitor] vs [Your Brand]” come from risk-averse buyers seeking reassurance. Review-focused pages with G2 badges, side-by-side feature comparisons, and customer quotes give them the confidence to book a demo.
Ad copy should align with these intent buckets so that the message in the ad matches the promise on the landing page. Effective cybersecurity conquesting ad templates include:
- “Tired of [Competitor] downtime? See why 500+ CISOs switched to [Your Brand]”
- “[Competitor] Alternative, 50% Lower TCO, Same Security Coverage”
- “Compare [Competitor] vs [Your Brand], Free Migration Included”
Performance Max campaigns support Search by reaching cybersecurity ABM audiences across Google’s inventory. They work best when they reinforce the same conquesting and intent-based strategy used in Search. Allocate about 45% of budget to competitor campaigns, 40% to generic terms, and 15% to brand protection. This mix creates coverage across high-intent competitor terms, scalable category searches, and defensive brand traffic.
Transform your cybersecurity lead generation with proven conquesting strategies. Let’s map these conquesting tactics to your specific competitor landscape.
Tracking, Budgeting, and Performance Assessment for Cybersecurity PPC
Conquesting tactics only deliver ROI when you can measure their impact accurately. That measurement foundation starts with a clear view of how Google Ads contribute to pipeline and revenue for B2B cybersecurity. Modest daily budgets can still produce competitive CPQL when campaigns target high-intent keywords and use strong conversion paths. Success requires the sophisticated CRM integration mentioned earlier, specifically HubSpot or Salesforce tracking that connects ad clicks to closed revenue.
Budget allocation usually follows company maturity stages and should align with the earlier 45/40/15 split across competitor, generic, and brand campaigns. Startups often begin with $5,000 in monthly spend and $1,250 management retainers. Growth and scale-stage companies increase budgets as they validate ROAS. Enterprise accounts frequently deploy $50,000 or more with dedicated team support. Properly tracked campaigns can reach 5.5x ROI when they include offline conversion implementation and revenue-based optimization. The framework below maps spend levels to realistic ROAS targets and management fees so you can benchmark your current performance against industry standards.
| Spend Band | Min. Budget/Day | Target ROAS | Management Fee |
|---|---|---|---|
| Startup ($5k-10k/mo) | $50 | 3x | $1,250 |
| Growth ($10k-25k/mo) | $150 | 4x | $1,750 |
| Scale ($25k-50k/mo) | $400 | 5x | $2,250 |
| Enterprise ($50k+/mo) | $800+ | 5.5x | $3,250 |
Attribution should use multi-touch models that connect first-touch awareness through final conversion. PPC-generated leads often show slightly lower MQL to SQL conversion rates than SEO leads, but they can recover with strong opportunity-to-close performance because of higher intent and better qualification.
Key tracking KPIs keep your focus on revenue instead of surface-level engagement. Net New ARR attributed to campaigns shows how much new recurring revenue your ads create. SQL volume and cost per SQL reveal how efficiently you turn ad clicks into real sales conversations. Pipeline velocity and deal size impact highlight whether paid traffic accelerates deals or increases average contract value. Customer acquisition cost by channel then compares paid search performance to other acquisition sources.
Common Pitfalls and Practical Optimization Strategies
Percentage-of-spend agencies often create misaligned incentives because they benefit from higher budgets regardless of performance. Flat-fee, month-to-month partnerships encourage agencies to re-earn business through results instead of long contracts, which better aligns with revenue-focused cybersecurity teams.
Common cybersecurity campaign mistakes usually start with targeting broad keywords without intent modifiers, which floods your funnel with unqualified traffic. That problem grows when teams send conquesting traffic to generic home pages that ignore the specific competitor pain points that triggered the search. Ignoring negative keyword hygiene for competitor terms then wastes budget on users who only want login pages or support resources. These tactical issues often stay hidden when reporting focuses on clicks and impressions instead of pipeline and revenue.
Conversion rate optimization can deliver 20 percent or more performance lifts when you apply heuristic analysis and build focused comparison pages. Cybersecurity companies like Watchcom achieved 55 percent CPC reductions and 80 percent lower cost per conversion by targeting competitor gaps with tailored messaging and landing experiences.
Two common internal scenarios often block progress. The overwhelmed founder spends weekends trying to manage campaigns without the time or data needed to improve them. The frustrated VP of Marketing battles vanity metric reports from existing agencies and struggles to connect spend to pipeline. Both situations benefit from specialized cybersecurity expertise, transparent flat-fee pricing, and reporting that centers on SQLs and Net New ARR.
Conclusion and Next Steps for Cybersecurity Google Ads
B2B cybersecurity Google campaigns deliver measurable ROI when they rely on competitor conquesting, CRM integration, and intent-based targeting. This blueprint shifts focus away from vanity metrics and toward Net New ARR and SQL generation through systematic testing and optimization.
SaaSHero’s flat-fee, month-to-month model aligns agency success with client revenue growth. The team’s cybersecurity experience and proven frameworks support scaling profitable campaigns while keeping acquisition costs under control.
Ready to implement this revenue-focused approach? Let’s audit your current campaigns and build your 30-day launch roadmap.
Frequently Asked Questions
What’s the minimum Google Ads budget for cybersecurity campaigns?
Cybersecurity companies can start with $500 to $1,000 in monthly budgets for pilot programs, although $5,000 or more per month usually provides enough data for meaningful optimization. Daily budgets below $50 restrict learning and testing in competitive cybersecurity verticals where CPCs often exceed $20 to $40 per click.
Do Google Ads work for B2B cybersecurity companies?
Yes, Google Ads generate strong ROI for cybersecurity companies when campaigns target the right intent and connect to clear conversion paths. As mentioned earlier, the 3x ROAS benchmark comes primarily from competitor conquesting campaigns that focus on high-intent keywords. Comprehensive tracking through CRM integration then proves pipeline attribution and revenue impact. Success also depends on specialized knowledge of cybersecurity buyer behavior and long sales cycles.
How long do cybersecurity Google Ads campaigns take to show results?
Most campaigns begin generating initial leads within 30 to 60 days, although full performance usually takes longer to stabilize. Cybersecurity sales cycles vary by industry vertical and deal size. Healthcare deals average 14.7 months from initial contact to signed contract. Proper attribution tracking reveals how campaigns influence opportunities throughout these extended buyer journeys.
What’s the difference between MQLs and SQLs in cybersecurity marketing?
Marketing Qualified Leads (MQLs) show engagement signals such as downloading security whitepapers or attending webinars. Sales Qualified Leads (SQLs) meet ideal customer profile criteria that include company size, industry, and demonstrated buying intent. Cybersecurity SQLs typically involve budget authority, specific security challenges, and clear implementation timelines.
How do you track ROI from cybersecurity Google Ads campaigns?
ROI tracking relies on CRM integration that connects ad clicks to closed revenue through platforms like HubSpot or Salesforce. Multi-touch attribution models then distribute credit across awareness, consideration, and decision touchpoints. Key metrics include Cost Per SQL, pipeline influenced by marketing, and Net New ARR attributed to campaigns, instead of vanity metrics such as clicks or impressions.

