
Key Takeaways for Cybersecurity SaaS Growth
- Shift focus from vanity metrics like clicks to revenue metrics such as SQL conversion rates and Net New ARR in cybersecurity SaaS marketing.
- Use LinkedIn ABM for CISO outreach and Google Ads competitor conquesting against leaders like CrowdStrike to capture high-intent leads.
- Apply dark funnel intelligence and intent data from Bombora and 6sense to map complex 6 to 18 month cybersecurity buying cycles.
- Improve performance with heuristic CRO, dedicated landing pages, and CRM attribution via HubSpot or Salesforce to reach payback targets faster.
- Partner with SaaSHero’s flat retainer model for senior-led execution and ARR growth, and explore how we can scale your cybersecurity revenue engine.
Executive Summary and Cyber SaaS Revenue Framework
The Cyber SaaS Revenue Playbook functions as a connected system built on seven strategic pillars. Each pillar uses data from the previous step to move buyers closer to revenue.
The framework starts by mapping buyer psychology through dark funnel intelligence. Once you understand where prospects research anonymously, you can intercept them with targeted campaigns and then attribute revenue accurately in your CRM.
- Map buyer psychology through dark funnel intelligence
- Run competitor conquesting campaigns that target searches for CrowdStrike alternatives and similar terms
- Deploy LinkedIn ABM to reach CISO level decision makers inside target accounts
- Refine Google Ads to capture high intent cybersecurity searches that signal active evaluation
- Apply heuristic CRO to remove friction and increase conversion efficiency on key pages
- Connect CRM and ARR attribution through HubSpot or Salesforce integration for full funnel visibility
- Scale operations through flat retainer partnerships that support predictable, senior led execution
Performance benchmarks include SQL conversion rates above 50 percent for top performers, payback periods under 12 months, and CAC to LTV ratios that support sustainable growth. These are not theoretical targets. SaaSHero has validated this framework across multiple cybersecurity verticals in real world implementations.
Cyber SaaS Buyer Landscape and Channel Strategy
Before applying the framework, you need a clear view of how cybersecurity buyers actually purchase. Cybersecurity buyers follow a complex, non linear journey shaped by risk, compliance, and internal security politics.
They spend most of this journey in anonymous research mode. They conduct dark funnel research across G2, LinkedIn, and vendor websites long before they fill out a form. Traditional attribution models struggle because 70% of the B2B buying journey happens anonymously.
This reality forces a shift from vanity metrics such as CTR and impressions to performance metrics like SQL volume and ARR contribution. Channel selection must reflect this shift. Dreamdata’s 2025 LinkedIn Ads Benchmarks Report showed LinkedIn Ads delivered 113 percent ROAS across their B2B customers, making it the only consistently profitable B2B paid platform in that dataset.
The table below shows how core channels align with buyer intent in cybersecurity. Use it to match your budget to the stage of the evaluation journey you want to influence.
| Channel | Intent Type | Cyber Example | CPL Benchmark |
|---|---|---|---|
| Google Ads | Pricing or Complaint | “CrowdStrike alternatives” | High, with strong deal quality |
| LinkedIn ABM | Firmographics | CISO targeting | High, with multi stakeholder influence |
SaaSHero’s platform agnostic approach uses this type of intent mapping to select channels based on performance data, not vendor relationships.
Key Tactics for Cybersecurity: Competitor Conquesting and ABM
Competitor conquesting captures buyers who already feel pain with an incumbent solution. It relies on three psychological intent buckets that reveal where a prospect sits in the evaluation process.
Pricing research searches such as “CrowdStrike pricing” signal budget checks and cost sensitivity. Problem or complaint searches indicate dissatisfaction and a higher chance of switching. Review validation searches show buyers who want proof before they commit, which often occurs late in the cycle.
Users who search “CrowdStrike alternatives” combine frustration with active switching intent. These queries often produce shorter sales cycles and higher close rates because the buyer already believes a change is necessary.
Effective conquesting requires dedicated landing pages with comparison tables, switching resources, and legal compliance review. These pages give prospects the side by side information they expect when they search for alternatives. Not every competitor search reflects real switching intent, so negative keyword hygiene becomes critical. It filters out navigational queries from people who only want the competitor’s login page and keeps spend focused on evaluative searches that indicate real consideration.
Conquesting focuses on buyers at the bottom of the funnel who already want a change. To influence earlier research and shape vendor shortlists, you need a complementary tactic that works higher in the funnel.
LinkedIn ABM fills that role by combining firmographic targeting with intent data from Bombora and 6sense. This combination reaches cybersecurity decision makers during active evaluation periods, even before they search for alternatives by name. AI-powered personalization then customizes messages at scale based on role, industry, and observed intent signals.
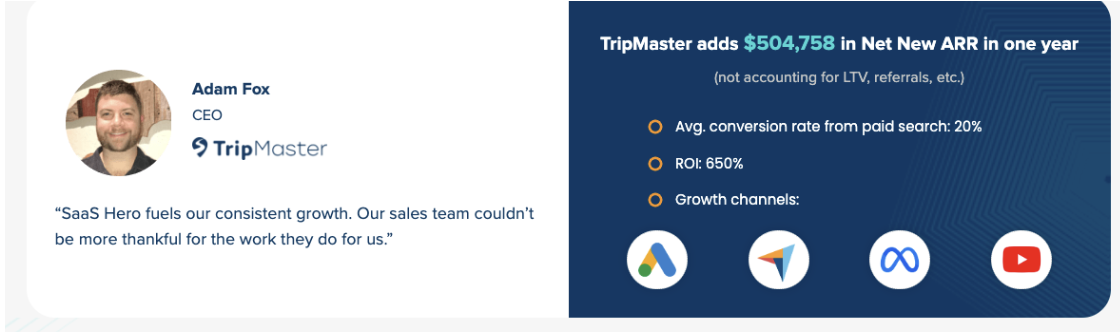
When you run conquesting and ABM together, you cover both in market buyers and accounts that are just entering research mode. SaaSHero’s cybersecurity case studies show ARR gains driven by this combined approach, with measurable improvements in conversion rates and cost per opportunity.
The table below summarizes how these tactics perform in typical cybersecurity engagements.
| Tactic | Competitor Context | SaaSHero Benchmark |
|---|---|---|
| Conquesting | CrowdStrike | Cost per lead reductions of 20 to 40 percent on high intent terms |
| ABM | Generic targeting | Lead to opportunity conversion rates that outperform generic campaigns by 30 percent or more |
Metrics, CRO, and Pipeline Repair for Cybersecurity SaaS
Revenue focused KPIs provide the foundation for every optimization decision. Core metrics include ARR growth, pipeline value, and SQL conversion rates tracked through HubSpot or Salesforce CRM integration.
Once you track the right metrics, heuristic CRO methodology helps you improve them. This approach identifies conversion barriers through 5 second tests, trust signal improvements, and mobile responsiveness audits that reflect how security buyers actually browse.
Pipeline diagnostic frameworks then address the vanity metric trap by tying every stage from ad click to closed revenue. Teams move from reporting on MQL volume to understanding MQL to SQL conversion rates, with top performers exceeding 50 percent when qualification rules and intent data align.
SaaSHero’s optimization work follows a clear maturity progression. Engagements start with an audit, move into quick wins that remove obvious friction, and then shift into systematic scaling once the unit economics support higher spend. This sequence produces conversion rate improvements and cost per lead reductions that hold as budgets grow.
Get your pipeline performance diagnosis through a discovery call and identify where revenue leaks occur today.
Why SaaSHero Fits Cybersecurity Performance Marketing
SaaSHero removes common agency friction points that slow cybersecurity growth. The team avoids percentage of spend billing, long term contracts, and junior account management that lacks domain context.
Our flat retainer model ranges from $1,250 to $7,000 monthly. Engagements run month to month and stay senior led, which keeps incentives aligned with performance instead of media volume.
Cybersecurity specialization brings deep knowledge of churn dynamics, compliance constraints, and CISO buying behavior. Case studies highlight ARR gains and payback periods that match investor expectations across several security categories, including endpoint, cloud, and identity.
Three engagement scenarios match different growth stages. Overwhelmed founders use the $1,250 tier to establish a working acquisition engine. Frustrated VPs move from underperforming agencies to regain control of pipeline. Post funding teams use SaaSHero to activate channels quickly without building a full in house team on day one.

FAQ
What are the most effective channels for cybersecurity SaaS performance marketing?
LinkedIn ABM and Google competitor conquesting consistently deliver strong ROI for cybersecurity SaaS when measured against revenue, not clicks. LinkedIn produces efficient ROAS through precise CISO and security leadership targeting. Google conquesting captures high intent users who research alternatives to incumbents like CrowdStrike. Email marketing and SEO then support the longer nurture cycles that often appear in security sales.
How do you fix a stalled cybersecurity SaaS pipeline?
Stalled pipelines usually come from a focus on vanity metrics and weak lead qualification. A practical fix combines competitor conquesting campaigns, heuristic CRO improvements, and revenue focused attribution that tracks performance to SQL and opportunity stages.
SaaSHero’s methodology has delivered measurable cost per lead reductions and higher conversion rates by shifting reporting from impressions and clicks to SQL and ARR impact.
What does SaaSHero pricing look like for $10K monthly ad spend?
For $10K in monthly ad spend, SaaSHero charges $1,250 monthly on a month to month basis or $1,000 with 6 month prepayment. This flat retainer model, described in more detail in the pricing section above, removes percentage of spend conflicts and keeps budget recommendations tied to performance data.
What are the key 2026 ABM trends for cybersecurity?
AI driven personalization leads 2026 ABM trends in cybersecurity. Teams use AI to tailor creative and messaging at scale for different roles, industries, and security postures.
Intent data integration from platforms like Bombora and 6sense supports precise timing of outreach. Companies that combine AI with intent informed ABM report pipeline efficiency gains compared to traditional static campaigns.
What are typical cybersecurity SaaS SQL conversion rates?
Cybersecurity SaaS SQL conversion rates vary based on offer quality, targeting, and qualification rules. Well structured programs achieve strong MQL to SQL conversion by combining behavioral scoring with intent data.
The most reliable results come from qualifying leads against a clear Ideal Customer Profile that includes company size, industry, security maturity, and decision maker authority.
Conclusion and Next Steps for Cybersecurity SaaS Teams
The cybersecurity SaaS performance marketing playbook relies on specialized expertise, revenue focused metrics, and consistent tactical execution. Teams that move beyond vanity metrics and track Net New ARR, SQL conversion rates, and pipeline velocity gain a clearer view of what truly drives growth.
SaaSHero’s flat retainer structure, cybersecurity focus, and documented case studies position the team as a strong performance partner for scaling security vendors. The framework described above has generated ARR growth for clients while keeping payback periods within acceptable ranges for SaaS investors.
Start implementing this revenue playbook and accelerate your ARR growth today.

