
Key Takeaways for Cybersecurity Growth
- Cybersecurity tech companies scaling from $1M to $10M ARR need intent-based marketing such as competitor conquesting and LinkedIn CISO ads, not broad generic tactics.
- Teams convert more buyers when they target CISOs, CIOs, and CFOs with content about AI threats, quantum compliance, and clear ROI justification.
- Revenue attribution dashboards should connect marketing activity to closed-won ARR, with CAC-to-LTV below 3:1 and payback periods under 90 days.
- Teams avoid wasted spend by focusing on qualified pipeline instead of vanity metrics, weak negative keyword management, and misaligned agency models.
- Partner with SaaSHero for proven cybersecurity marketing strategies and start building your 90-day growth roadmap with a discovery call.
Strategic Context: 2026 Threats Push Buyers Toward Intent-Driven Research
The cybersecurity buying landscape has fundamentally shifted in 2026. Eighty-seven percent of security professionals report more AI-driven threats, which creates urgency to upgrade defenses without triggering impulsive purchases.
Many B2B cybersecurity buyers now consume several pieces of content before contacting sales, and they need multiple touchpoints before conversion. This extended research phase pushes marketers to intercept prospects during high-intent moments instead of relying on broad awareness campaigns that rarely convert.
The most effective cybersecurity marketing strategies in 2026 focus on prospects who compare solutions, research pricing, or seek alternatives to current vendors. Companies using competitor conquesting strategies see 3x higher conversion rates than those relying on generic keyword targeting, so intent-based marketing has become essential for efficient growth.
Executive Summary: 9 Tactics Built for High-Intent Cybersecurity Buyers
Because cybersecurity buyers conduct deep independent research and face urgent AI-driven threats, the 9 tactics below focus on intercepting high-intent prospects during active evaluation instead of chasing broad awareness.
The following 9 tactics work together as a digital marketing framework for cybersecurity tech companies:
- Competitor conquesting campaigns
- LinkedIn CISO-targeted advertising
- AI threat-focused content marketing
- G2 and review site optimization
- Heuristic conversion rate optimization
- Negative keyword management
- Email nurture sequences
- Quantum compliance messaging
- ARR attribution dashboards
Success metrics center on revenue impact, not surface-level engagement. Target CAC-to-LTV ratios below 3:1, ARR payback periods under 90 days, and pipeline attribution that connects first-touch marketing to closed-won deals. This framework emphasizes intent-driven traffic and CRM integration so your team can follow prospects from initial ad click through contract signature.
Cybersecurity Buyer Landscape: Personas and the Dark Funnel
Primary buyer personas for B2B cybersecurity solutions include CISOs, CIOs, IT directors, security operations managers, security architects, legal officers, procurement heads, and CFOs. These roles form a buying committee, and each persona brings distinct concerns and decision criteria.
Risk-averse CISOs focus on measurable risk reduction and compliance with frameworks such as NIST and GDPR. Compliance fears often center on HIPAA, PCI-DSS, and SOC 2, while IT directors worry about integration challenges and workflow efficiency. CFOs scrutinize ROI and budget predictability and expect clear justification for every security investment.
The extended research phase described earlier plays out mainly in the dark funnel through G2 reviews, LinkedIn research, and peer recommendations. Security buyers evaluate solutions independently and with skepticism before vendor conversations. Effective marketing strategies account for this hidden research and provide value at each touchpoint buyers choose.
The table below shows how each core persona’s concerns map to specific channels, which reveals where to intercept buyers during their research.
| Persona | Primary Concerns | Preferred Channels |
|---|---|---|
| CISO | Risk reduction, compliance | Google Ads pricing searches |
| IT Director | Integration, workflow efficiency | LinkedIn reviews and research |
| CFO | ROI, budget predictability | Vendor comparison content |
Key Decisions: Channel Mix and Agency Trade-offs
Successful cybersecurity marketing usually allocates about 80% of budget to Google Ads and LinkedIn, which serve as the highest-intent channels for B2B security buyers. Paid search delivers competitive CAC for high-intent searches, while LinkedIn Ads average $982 CAC for B2B audiences.
Agency selection shapes performance and spend efficiency. Traditional percentage-of-spend models create misaligned incentives because they reward higher budgets instead of better results. SaaSHero’s flat retainer model ($1,250-$5,750 per month) removes this conflict so recommendations focus on performance, not fee maximization.
Poor attribution remains a critical risk for cybersecurity marketers. Many agencies report impressions and clicks but fail to connect marketing spend to closed-won revenue. SaaSHero’s HubSpot and Salesforce integrations track prospects from first ad click through contract signature, which provides clear ROI visibility for cybersecurity marketing investments. With proper attribution in place, you can deploy the following 9 tactics and know exactly which efforts drive revenue.
Cybersecurity Marketing Strategies: 9 Revenue-Proven Tactics for 2026
1. Competitor Conquesting Campaigns
Competitor conquesting targets prospects who actively research alternative solutions, so your team captures high-intent traffic when buyers feel most open to switching. SaaSHero’s conquesting playbooks have delivered significant ROI improvements by targeting competitor pricing pages and alternative searches.
Strong conquesting campaigns segment by search intent such as pricing queries, problem intent, and validation searches. Each intent type needs its own landing page with specific messaging and a clear value proposition that addresses the related pain point.
2. LinkedIn CISO-Targeted Advertising
LinkedIn offers precise targeting for cybersecurity decision-makers. As noted earlier, LinkedIn’s average $982 CAC for B2B audiences makes it cost-effective for cybersecurity campaigns, especially when paired with high buyer intent and clear targeting criteria.
Effective LinkedIn campaigns target specific job titles such as CISO and Security Director, along with company sizes between $10M and $100M in revenue and defined industry verticals. Ad creative should speak to current threat landscapes, compliance requirements, and ROI justification instead of generic security claims.
3. AI Threat-Focused Content Marketing
Attackers now harvest encrypted data for future decryption with quantum tools, which raises urgency for quantum-safe security solutions. Content that explains the 2026 threat landscape captures attention from security professionals who seek current intelligence.
High-performing topics include AI-powered attack vectors, quantum-safe cryptography, and updates to compliance frameworks. Case studies strongly influence cybersecurity purchase decisions, so threat-specific case studies often become high-value lead generators.
4. G2 and Review Site Optimization
Review site optimization often produces results within one to two months and scales well for category leaders. G2 and Capterra act as core research hubs for cybersecurity buyers who compare solutions.
Winning strategies include asking satisfied customers for detailed reviews, responding to negative feedback with professionalism, and keeping product information current. Strong review scores and active responses signal reliability to risk-averse security buyers.
5. Heuristic Conversion Rate Optimization
Cybersecurity landing pages must establish trust and credibility within seconds. Eighty-two percent of cybersecurity buyers prioritize trust over price when they evaluate solution providers, so page design and messaging directly affect conversion rates.
Heuristic analysis helps teams spot conversion barriers before they invest in expensive A/B tests. Key elements include clear value propositions, visible trust signals such as certifications and customer logos, and friction-free demo requests. Security-specific trust signals include compliance badges, penetration testing results, and security certifications.
6. Strategic Negative Keyword Management
Negative keywords protect budgets from irrelevant traffic. For cybersecurity campaigns, common negative keywords include “free,” “open source,” and competitor brand names without modifiers. This filtering keeps spend focused on qualified prospects instead of researchers or existing customers who only want login pages.
7. Email Nurture Sequences
Email marketing delivers strong ROI in B2B, so nurture sequences matter for long cybersecurity sales cycles. Effective sequences share ongoing threat intelligence, compliance updates, and educational content that maintains engagement between first touch and purchase decision.
8. Quantum Compliance Messaging
NIST now urges organizations to adopt quantum-safe algorithms and cryptographic agility in response to quantum computing threats. Messaging that addresses quantum readiness and compliance preparation resonates with forward-thinking security leaders.
9. ARR Attribution Dashboards
Revenue attribution connects marketing activities to closed-won deals so teams can allocate budget based on data. As mentioned earlier, proper attribution significantly improves ROI measurement, and Multi-Touch Attribution delivers 37% higher accuracy than single-touch models.
Effective attribution follows the complete buyer journey, from the first marketing touchpoint through all nurture interactions to the final contract. This visibility supports confident scaling of high-performing channels and helps teams cut wasteful spend. The table below compares expected ROI and implementation examples for three of the highest-impact tactics, giving you benchmarks to evaluate your own campaigns.
| Tactic | Cybersecurity Example | Expected ROI |
|---|---|---|
| Competitor Conquesting | Target “Palo Alto pricing” searches | Significant ROI improvement |
| LinkedIn CISO Ads | Target security directors at $50M+ companies | $982 avg CAC |
| Email Nurture | Threat intelligence newsletters | Strong ROI |
Ready to implement these tactics for your cybersecurity tech company? Discuss your growth objectives with SaaSHero’s cybersecurity marketing team and learn how our strategies can accelerate your path to $10M ARR.
SaaSHero Case Studies: Cyber and Tech ARR Wins
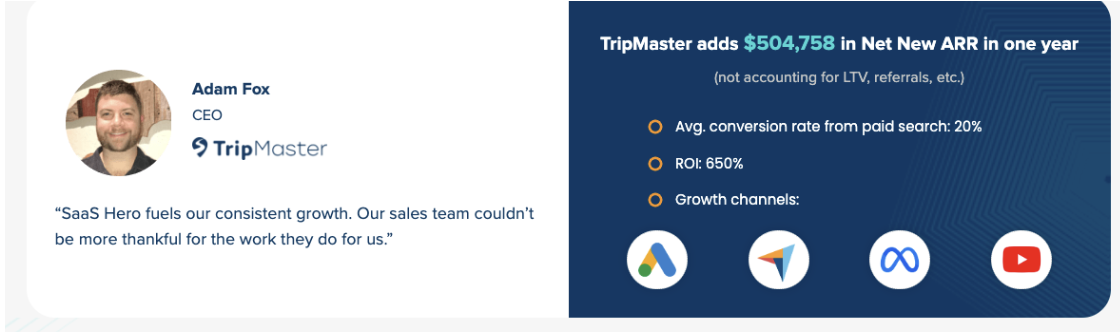
SaaSHero’s cybersecurity and technology marketing expertise has generated substantial ARR growth for clients across the sector. TripMaster achieved $504,758 in Net New ARR through strategic paid search and social campaigns paired with conversion rate optimization.
TestGorilla reached an 80-day payback period while scaling to support a $70M Series A raise. This efficiency shows the impact of properly attributed marketing spend focused on qualified pipeline generation instead of vanity metrics.
Playvox cut cost per lead by 10x through account restructuring and negative keyword optimization. This improvement highlights how strategic campaign management can unlock major efficiency gains for cybersecurity tech companies.
These results show SaaSHero’s ability to scale cybersecurity tech companies while protecting unit economics. The focus on Net New ARR and payback periods aligns with the metrics that matter most to cybersecurity founders and investors.
Common Pitfalls and Diagnostics: Five Traps to Avoid
Cybersecurity marketing failures usually come from five related pitfalls that share a root cause of misaligned incentives and weak measurement. Percentage-of-spend agency models create the most fundamental problem because they reward budget inflation instead of efficiency. This misalignment often leads directly to vanity metric reporting that highlights clicks and impressions while ignoring pipeline impact and closed-won revenue.
Teams that skip competitor conquesting leave high-intent traffic for rivals. Many cybersecurity companies focus only on branded keywords while competitors capture prospects who actively seek alternatives. Weak attribution then hides which channels drive real revenue growth, so budgets drift toward noise.
Generic messaging creates the final failure pattern. Content that ignores cybersecurity-specific concerns such as compliance requirements, integration challenges, and risk reduction rarely resonates. Security buyers expect specialized content that addresses their unique pain points and decision criteria.
Diagnostic questions include: Is your CAC-to-LTV ratio above 3:1? Are you tracking marketing attribution to closed-won deals? Do you have competitor conquesting campaigns running? If you answered no to any of these questions, get your free marketing audit to identify exactly where your campaigns leak revenue.
B2B Marketing for Cyber SaaS: Scenarios and Implementation Paths
Cybersecurity marketing strategies should match company stage and target market. Bootstrap founders often start with competitor conquesting and LinkedIn ads so they can stretch limited budgets toward high-intent opportunities. Series A companies usually expand into multi-channel programs that add content marketing and email nurture sequences for scale.
Enterprise-focused cybersecurity companies need longer nurture cycles and higher-touch sales processes. Because enterprise buyers require extensive education before they commit to complex solutions, these companies benefit from webinar programs that deliver deep technical content while qualifying attendee interest. Webinars convert attendees into qualified sales leads and work especially well for complex cybersecurity solutions that require demonstration and explanation. Executive content and account-based marketing that targets specific prospect accounts round out this enterprise motion.
SMB-focused cybersecurity companies can move faster because they work with shorter sales cycles and lower price points. These teams often succeed with direct-response campaigns, free trial offers, and self-service onboarding that supports rapid adoption.
Conclusion: Turn Strategy into a 90-Day Cybersecurity Growth Plan
The 9 tactics in this guide form a practical framework for scaling cybersecurity tech companies from $1M to $10M ARR. Teams that win focus on intent-driven marketing, accurate attribution, and revenue-focused metrics instead of vanity measurements.
Most companies see quick impact by starting with competitor conquesting and LinkedIn CISO targeting, then layering content marketing and email nurture for sustained growth. Attribution tracking from day one ensures every marketing investment ties back to measurable ARR.
Ready to accelerate your cybersecurity tech growth? Develop your customized 90-day marketing roadmap with SaaSHero’s team, starting with a discovery call to discuss your specific challenges.
Frequently Asked Questions
What is the most effective digital marketing channel for cybersecurity tech companies?
Competitor conquesting through Google Ads consistently delivers strong ROI for cybersecurity companies. This strategy targets prospects who actively research alternatives to current solutions, so your team captures high-intent traffic when buyers feel ready to switch. Effective conquesting campaigns segment by search intent and use dedicated landing pages that address specific pain points. Companies that implement competitor conquesting strategies often see 3x higher conversion rates than those using generic keyword targeting.
How long does it take to see results from cybersecurity marketing campaigns?
Paid advertising campaigns can generate qualified leads within two to four weeks, while organic strategies such as content marketing and SEO usually need three to six months for significant impact. The cybersecurity sales cycle often spans three to nine months depending on deal size and complexity, so marketing attribution must account for extended nurture periods. Companies should expect multiple touchpoints before conversion, which makes sustained multi-channel campaigns essential.
What metrics should cybersecurity companies track for marketing ROI?
Teams should focus on revenue-focused metrics instead of vanity measurements. Key metrics include Net New ARR attributed to marketing, CAC-to-LTV ratios below 3:1, and payback periods under 90 days. Pipeline velocity, lead-to-customer conversion rates, and marketing-influenced revenue also matter. Multi-touch attribution models provide the most accurate ROI measurement because they distribute credit across multiple touchpoints in the extended B2B buying journey.
How should cybersecurity companies approach competitor conquesting campaigns?
Teams should segment competitor campaigns by search intent such as pricing queries, problem or complaint searches, and review or validation searches. Each intent type needs a dedicated landing page with relevant messaging and a clear value proposition. Negative keywords help filter out navigational searches so budgets focus on evaluative queries. Campaigns should target competitor pricing pages, alternative searches, and comparison keywords while avoiding trademark violations through factual comparisons only.
What content formats work best for cybersecurity buyer personas?
Case studies often influence cybersecurity purchase decisions, so they serve as a high-impact content format. Webinars convert attendees into qualified leads and work especially well for complex solutions that require education. White papers, threat intelligence reports, and compliance guides build trust with technical buyers. Email nurture sequences deliver strong ROI and help maintain engagement during extended sales cycles. All content should address specific cybersecurity concerns such as compliance requirements, threat landscapes, and risk reduction instead of generic business benefits.

