
Key Takeaways
- Ransomware attacks rose 15% in 2024, and over one-third of breaches came through third parties, so Cyber SaaS teams must secure CRM-marketing integrations.
- A 7-step framework that includes security audits, zero-trust data mapping, and continuous monitoring protects sensitive prospect data across revenue systems.
- Top threats like AI-powered ransomware, OAuth abuse, and shadow SaaS require concrete controls such as least-privilege access and AI-resistant logging.
- Secure integrations accelerate pipeline growth, shorten sales cycles by about 25%, and support 2026 compliance with GDPR, CCPA, and the EU AI Act.
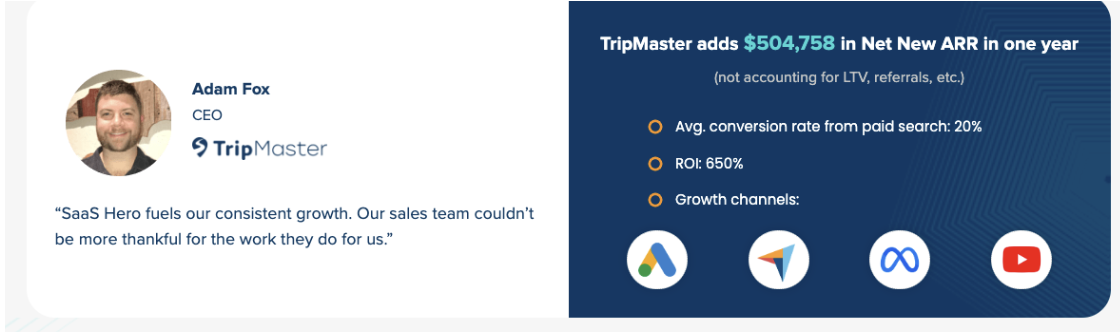
- Partner with SaaSHero for a comprehensive security audit to reach outcomes like $504k Net New ARR while scaling revenue safely.
Prerequisites for Secure CRM-Marketing Integrations
Cybersecurity SaaS companies need a few foundations in place before they secure CRM-marketing integrations. Teams require administrative access to their CRM platform such as HubSpot or Salesforce, an existing marketing automation setup, executive approval for security protocols, and baseline security audit capabilities.
Revenue teams should also define core metrics like Customer Acquisition Cost (CAC), Lifetime Value (LTV), Net New Annual Recurring Revenue (ARR), and Sales Qualified Leads (SQLs). Compliance requirements for 2026 include GDPR and CCPA evolutions with enhanced AI governance requirements, plus the EU AI Act’s risk-based framework for AI systems in customer interactions.
Common pitfalls include dark funnel attribution gaps, shadow SaaS proliferation, and over-permissioned OAuth grants. Most teams complete comprehensive security hardening in four to six weeks once these prerequisites exist.
What is CRM in Cyber Security? Top 7 Threats and Prevention
CRM cybersecurity protects customer and prospect data inside sales and marketing technology stacks while keeping revenue operations efficient. Integrating CRM systems with marketing automation expands the attack surface, so teams must apply targeted security controls across every connection.
| Threat | 2024-2026 Statistics | Primary Mitigation |
|---|---|---|
| AI-Powered Ransomware | Reported ransomware attacks increased 15% worldwide in 2024 | AI-monitored backups with zero-trust architecture |
| Third-Party Breaches | SecurityScorecard’s 2025 Global Third-Party Breach Report found that 35.5% of 1,000 analyzed 2024 data breaches originated via third parties | Least privilege OAuth with vendor vetting |
| Cloud Misconfigurations | Terabyte-scale data exposure | Multi-cloud IAM role alignment |
| AI Data Poisoning | Model corruption via tainted datasets | Data pipeline validation and monitoring |
| Shadow SaaS Sprawl | Uncontrolled data collection | Continuous SaaS discovery and governance |
| OAuth Token Abuse | Persistent broad permissions | Token lifecycle management with monitoring |
| Deepfake Social Engineering | Voice and video simulation attacks | Multi-factor authentication with biometrics |
These seven threat categories shape every phase of secure CRM-marketing integration. The framework below addresses each threat type with specific security controls at defined implementation stages so revenue systems stay protected end to end.
7-Step Secure Framework Overview
The secure CRM-marketing integration framework follows seven core phases that protect sensitive cybersecurity prospect data while supporting automated revenue growth. The table below maps each phase to its primary security action and revenue impact so teams can see how each control contributes to pipeline performance.
| Step | Primary Action | Revenue Impact |
|---|---|---|
| 1. Security Audit | Heuristic vulnerability assessment | Baseline SQL measurement |
| 2. Platform Selection | Risk-scored tool evaluation | Foundation for scaling |
| 3. Data Mapping | Secure field-level permissions | Compliance-ready flows |
| 4. Workflow Automation | Encrypted nurture sequences | Pipeline velocity increase |
| 5. Monitoring | AI-resistant audit logging | Improved lead qualification |
| 6. Vendor Risk Management | Vendor access and DPA controls | Reduced third-party breach exposure |
| 7. Revenue Optimization | Security-aligned revenue analytics | Higher win rates and payback clarity |
Step-by-Step: Implement Secure CRM Integrated Marketing Cybersecurity
Step 1: Conduct a Comprehensive Security Audit
Teams start with a systematic security assessment of existing CRM and marketing systems. Document all data collection methods, storage locations, usage purposes, and third-party sharing relationships so compliance responses stay fast and accurate.
This documentation then supports a full inventory of current integrations, API connections, and user access levels across every revenue system. The audit reveals which systems, users, and workflows require security hardening first.
Step 2: Select Security-Hardened Platforms
Revenue leaders evaluate CRM and marketing automation platforms based on 2026-ready security capabilities. Security now ranks as a primary buying factor for sales and marketing software, often ahead of feature depth or price.
The comparison table below highlights how leading platforms differ on security posture, integration complexity, and SaaSHero implementation tiers so teams can choose a stack that supports both growth and protection.
| Platform | 2026 Security Score | Integration Complexity | SaaSHero Tier Pricing |
|---|---|---|---|
| HubSpot | High (native MFA) | Excellent | $1,250/mo starting |
| Salesforce | Medium (AI risks) | Complex | Custom implementation |
| Pipedrive | Medium | Moderate | Standard tier available |
Step 3: Implement Zero-Trust Data Mapping
Apply least privilege principles with role-based permissions across record-level, field-level, and action permissions. Map sensitive data flows between systems and define encryption standards for data in transit and at rest.
Teams then configure granular field-level security that hides deal amounts, commission rates, and competitive intelligence from unauthorized users. This mapping enforces zero-trust controls while keeping sales and marketing productive.
Step 4: Deploy Secure Marketing Automation
Revenue teams build encrypted marketing workflows that nurture cybersecurity prospects through long sales cycles without exposing sensitive data. AI-driven automated personalization tailored to industry threats and compliance needs increases meetings booked and keeps messaging relevant.
Teams also implement secure lead scoring models that highlight high-intent prospects while preserving data privacy across every campaign and integration.
Step 5: Establish Continuous Security Monitoring
Enable comprehensive audit trails that automatically log all CRM data access and changes so incident investigations and compliance reviews stay grounded in reliable evidence.
Security teams monitor for suspicious access patterns, unusual API call volumes, and unauthorized data exports. Real-time alerts across integrated systems help teams contain threats before they affect pipeline or customer trust.
Step 6: Configure Vendor Risk Management
Evaluate vendor access scope, identity support such as SSO and granular roles, data handling practices, and operational maturity. These checks reduce exposure to third-party incidents mentioned earlier.
Teams then establish Data Processing Agreements with all marketing technology vendors and maintain evidence trails for regulators. This structure keeps CRM and marketing stacks aligned with privacy and security expectations.
Step 7: Optimize for Revenue Performance
Security leaders measure implementation success through revenue metrics instead of vanity indicators. Teams track secure SQL generation, protected pipeline value, and compliant conversion rates across each stage.
Win rates for qualified opportunities become a key benchmark once security and nurturing systems operate together. This step also connects directly to the secure workflows described next, where automation and sales execution translate controls into revenue.
Secure Workflows for Cybersecurity Sales Cycles
Cybersecurity sales teams need automation workflows that balance aggressive prospecting with strict data protection. Revenue teams implement encrypted competitor conquesting campaigns that reach prospects researching alternative solutions while staying aligned with privacy regulations.
They also deploy secure nurture sequences that educate prospects about threat landscapes and compliance requirements without revealing internal security details. These workflows build trust and keep deals moving.
Teams configure lead scoring models that surface high-intent cybersecurity buyers based on behaviors such as whitepaper downloads, compliance checklist requests, and threat assessment tool usage. AI conversation intelligence that analyzes calls for cybersecurity pain points and buying signals can shorten sales cycles by 25% once those high-intent leads reach sales.
These insights create value when secure handoff protocols preserve them during the marketing-to-sales transition. Handoffs must protect prospect privacy while giving sales teams clear context on security concerns, compliance deadlines, and competitive evaluations.
Why SaaSHero Leads Secure CRM Integrated Marketing
SaaSHero focuses on secure CRM-marketing integrations for cybersecurity SaaS companies and ties every project to measurable revenue outcomes. Flat-fee retainers starting at $1,250 monthly with month-to-month agreements remove the conflicts that percentage-based agency models create.
The team brings deep vertical knowledge across HR Tech, Transportation, Procurement, Healthcare, Construction, Marketing Tech, and Cybersecurity sectors. Proven results include $504k Net New ARR for TripMaster and 80-day payback periods for TestGorilla, which shows how secure CRM-marketing integrations translate directly into revenue performance.
Unlike generalist agencies that chase vanity metrics, SaaSHero integrates into client communication systems such as Slack and Google Chat. Reporting focuses on Net New ARR, Pipeline Value, and Sales Qualified Leads instead of clicks and impressions.
Schedule your security implementation audit to deploy enterprise-grade CRM security while accelerating revenue growth.
Measure Success and Stay 2026 Compliant
Teams measure security success through revenue-focused metrics such as secure SQL generation rates, protected pipeline value, compliant conversion percentages, and time-to-close for security-qualified opportunities. Maintain vendor due diligence including Data Processing Agreements, security control confirmations, and sub-processor documentation for every CRM and marketing technology provider.
Automated compliance monitoring should track consent management, data retention schedules, and deletion protocols across integrated systems. Regular security audits then review OAuth token lifecycle management, API access patterns, and integration permission drift so the security posture stays strong over time.
Recap and FAQ: Secure Your CRM Marketing Now
Secure CRM integrated marketing cybersecurity relies on zero-trust principles, vendor risk management, and continuous monitoring across every revenue system. The seven-step framework protects sensitive cybersecurity prospect data while supporting automated pipeline growth and alignment with 2026 privacy regulations.
How long does secure CRM-marketing integration setup take?
Comprehensive security hardening typically requires four to six weeks for initial implementation. This period covers security audits, platform configuration, workflow deployment, and monitoring system activation.
The exact timeline depends on current system complexity, data volumes, and regulatory obligations in each market.
What are the biggest security risks in CRM-marketing integrations?
Primary risks include third-party vendor breaches, which accounted for over one-third of 2024 incidents as noted earlier. AI-powered ransomware also continues to grow at double-digit rates.
Additional risks include OAuth token abuse through over-permissioned integrations and shadow SaaS proliferation that creates unmonitored data flows across the stack.
How do secure integrations impact revenue performance?
Properly secured CRM-marketing integrations improve lead qualification through AI-safe automation and increase meetings booked through compliant personalization. Secure conversation intelligence then helps teams shorten sales cycles by about 25% while preserving regulatory compliance.
What compliance frameworks apply to cybersecurity CRM systems?
Key frameworks include GDPR with 72-hour breach notification requirements and CCPA or CPRA with enhanced AI governance provisions. The EU AI Act governs automated decision-making systems, and industry-specific standards such as SOC 2 apply to many SaaS providers.
How can cybersecurity companies scale secure marketing automation?
Scaling secure automation requires a zero-trust architecture with least privilege access and continuous SaaS discovery and governance. Teams also need encrypted automation workflows and revenue-focused monitoring that tracks secure pipeline generation instead of vanity metrics.
Start with a compliant CRM security assessment to protect your revenue systems while achieving measurable growth outcomes.

