
Key Takeaways for Cybersecurity CRO
- Cybersecurity SaaS landing pages often underperform because risk-averse buyers want visible proof of compliance and security certifications before they convert.
- Use a four-stage CRO framework that includes heuristic audits, hero section optimization, trust signal integration, and conversion defense to move conversion rates from 1–2% toward stronger performance.
- Focus on security-first hero messaging, prominent SOC2 and ISO badges, and streamlined forms with clear privacy assurances to increase conversions.
- Support growth with competitor conquest pages, security-focused social proof, and lead magnets such as compliance checklists that attract high-intent prospects.
- Partner with SaaSHero for proven cybersecurity CRO expertise and plan a revenue-focused CRO strategy session that can accelerate ARR growth.
Executive Summary and Core Concepts for Security CRO
Conversion rate optimization for cybersecurity landing pages depends on understanding the specific buyer journey in this vertical. Cybersecurity buyers spend more time in evaluation than typical B2B SaaS buyers, and they involve stakeholders across IT, security, compliance, and procurement.
The four-stage framework for cybersecurity CRO success includes:
- Heuristic Audit: Systematic evaluation against cybersecurity-specific usability and trust principles.
- Hero Section Optimization: Trust-first messaging that addresses security concerns immediately.
- Trust Signal Integration: Strategic placement of certifications, compliance badges, and social proof.
- Conversion Defense: Friction reduction while preserving essential security messaging.
CRO in cybersecurity focuses on high-intent prospects who already completed extensive research before visiting your page. The objective is turning these qualified visitors into sales-qualified leads despite their skepticism and risk sensitivity. Industry benchmarks show cybersecurity landing pages often convert below their potential, significantly under the performance achievable through specialized optimization.
Cybersecurity SaaS Landing Page Landscape in 2026
The cybersecurity buyer journey in 2026 features extensive dark funnel research across many channels. Prospects review content on G2, Capterra, vendor comparison sites, and peer communities long before they engage directly with vendors.
This research-heavy behavior reflects the high stakes of cybersecurity decisions. A poor vendor choice can trigger data breaches, compliance failures, and major financial losses. IBM reports the global average cost of a data breach at $4.88 million in 2024, so security leaders approach vendor selection with extreme caution.
These high stakes push buyers to demand messaging that addresses current, concrete threats instead of generic security promises. The shift from broad security language to AI-threat-specific positioning reflects this change in expectations. Panorays identifies AI-amplified social engineering as a dominant trend, including voice cloning and deepfake videos, so landing pages must speak directly to these risks.
Primary traffic channels for cybersecurity SaaS include Google Ads competitor campaigns, LinkedIn campaigns targeting security roles, and organic search from branded and comparison queries. LinkedIn Ads show average landing page conversion rates of 2–5%, which highlights the value of channel-specific optimization strategies for security audiences.
10 CRO Tactics Organized by the Four-Stage Framework
Stage 1: Heuristic Audit and Diagnostic Foundation
1. Implement a Cybersecurity Heuristic Audit Framework
Run a structured heuristic analysis before launching A/B tests so you fix obvious issues first. This analysis should evaluate four dimensions that directly influence security buyer confidence and willingness to convert.
First, assess relevance and confirm that the page matches security-focused ad copy and search intent. Next, evaluate clarity and confirm that the value proposition and security benefit appear immediately. Then review trust signals and verify that certifications and compliance badges appear above the fold. Finally, identify friction points and confirm that forms and flows feel safe and respectful for security-conscious users.
Stage 2: Hero Section Optimization and Conquest Strategy
2. Write Hero Sections with Explicit Security Messaging
Lead with security-first headlines that speak to outcomes, such as “Secure Your Stack in 5 Minutes” or “Zero-Trust Architecture Made Simple.” Place security benefits and risk reduction statements before feature lists so risk-averse buyers see reassurance as soon as the page loads.
3. Build Competitor Conquest Landing Experiences
Create dedicated pages that target searches such as “[Competitor] alternatives” or “[Competitor] pricing.” Address known weaknesses of established players like CrowdStrike or Wiz, and support your claims with specific case studies from customers who switched to your platform.
Stage 3: Trust Signal Integration and Social Proof
4. Place Trust Signals Where Decisions Happen
Position security certifications, compliance badges, and customer logos close to forms, pricing sections, and primary calls to action. Research from multiple sources shows that trust signals influence conversions in different ways. Unbounce reports that SOC2 and ISO certifications can increase conversions, while HubSpot notes similar gains from G2 badges. Invesp finds that customer logos deliver mixed results, which suggests their impact depends on logo recognition and placement.
5. Design Forms for Security-Sensitive Visitors
Limit form fields to essential details so security buyers do not feel overexposed. Research shows three-field forms convert at 25%, while seven-field forms convert at 12%, which illustrates the cost of unnecessary friction. Add security-specific copy such as “Your data is encrypted and never shared” near the form button to reduce anxiety.
6. Highlight Security-Focused Social Proof
Show testimonials that reference concrete security outcomes instead of vague satisfaction claims. Examples include statements such as “Zero successful attacks in 6 months” or “Passed SOC2 audit with no critical findings after rollout.” Research shows that detailed case studies strongly influence cybersecurity purchase decisions.
Stage 4: Conversion Defense, Mobile Experience, and Traffic Quality
7. Apply Mobile-First Security Layouts
Ensure that security messaging, certifications, and key trust elements appear clearly on mobile screens. Seventy-nine percent of SaaS landing page traffic comes from mobile devices, so responsive layouts that preserve trust signals play a direct role in conversion performance.
8. Use Negative Keywords to Protect Budget
Refine paid search campaigns by excluding low-intent navigational searches such as a competitor name alone. Focus spend on evaluative searches like “[competitor] alternatives” or “[competitor] pricing,” which signal active comparison and higher purchase intent.
9. Prioritize Security-Focused A/B Tests
Test security-first headlines against feature-first versions, experiment with different certification placements, and compare short versus long forms. Personalized CTAs perform 202% better than generic ones, so tailor calls to action for security roles, use cases, and funnel stages.
10. Offer Security-Themed Lead Magnets
Provide compliance checklists, threat assessment templates, or security framework guides as gated resources. These assets match how cybersecurity buyers research solutions and give your team contact information for targeted nurturing sequences.
SaaSHero’s Revenue-First Cybersecurity CRO Approach
SaaSHero focuses on cybersecurity SaaS CRO and delivers consistent performance gains across this vertical. Our cybersecurity clients see average conversion rate improvements above 20%, with case studies showing 650% ROI and $504k in Net New ARR generation. This performance comes from deep vertical expertise and a clear understanding of security buyer psychology.
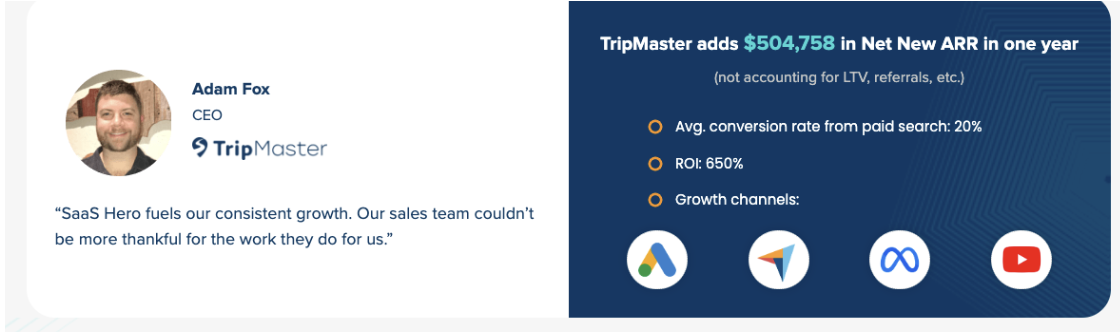
Our flat-rate retainer model starting at $1,250 per month removes conflicts that appear with percentage-of-spend pricing. Month-to-month agreements keep performance accountability high, and our cybersecurity-specific heuristic audits uncover conversion barriers that generalist agencies often miss.
The SaaSHero model also includes dedicated landing page builds at $750 per page, which sits below typical market rates for cybersecurity-focused design. This investment supports stronger campaign performance and higher customer lifetime value. Our team understands compliance requirements, security certification messaging, and the complex stakeholder dynamics that shape cybersecurity sales cycles.

Explore a tailored CRO engagement to see how our cybersecurity methodology can transform landing page performance and accelerate pipeline growth.
Common Cybersecurity Landing Page Pitfalls and Diagnostics
Cybersecurity landing pages often fail for predictable reasons that trace back to misunderstanding security buyer priorities. The most fundamental mistake involves weak message match between ads and landing pages, which confuses visitors who expect consistent security claims. This confusion grows when security certifications are absent or buried, because buyers cannot quickly confirm vendor trustworthiness.
Generic SaaS messaging that ignores cybersecurity-specific pain points also weakens performance. Overly complex forms that request unnecessary personal or company data create friction for privacy-conscious prospects. Vague testimonials and case studies that lack security metrics further reduce credibility with technical audiences who expect evidence.
Use a simple self-audit to identify these issues. Confirm that your headline addresses security concerns immediately and that SOC2 or ISO certifications appear above the fold. Review testimonials for specific security metrics, such as incident reduction or audit outcomes. Check whether your form respects privacy expectations and whether your page loads in under two seconds so security-minded visitors do not abandon the experience.
Implementation Scenarios for Cybersecurity Teams
Two primary archetypes benefit most from specialized cybersecurity CRO support. The overwhelmed founder scenario involves CEOs of growing cybersecurity startups who manage marketing while scaling from $500k to $2M ARR. These leaders need proven frameworks and hands-on execution so they can improve conversion rates without building a large internal team.
The frustrated VP of Marketing scenario involves experienced leaders at Series B and later-stage cybersecurity companies who feel constrained by generic agency tactics. These teams need partners who understand CISO concerns, compliance requirements, and security architecture language while still delivering measurable pipeline impact.
Discuss your CRO roadmap with our team to uncover quick-win tests and longer-term optimization opportunities tailored to your growth stage.
Conclusion and Next Steps for Security-Focused CRO
Cybersecurity SaaS landing page improvement requires specialized expertise that aligns with the psychology and priorities of security buyers. By applying the framework in this guide, from heuristic audits through trust signal integration and conversion defense, cybersecurity companies can reach conversion benchmarks that support sustainable growth in competitive markets.
Success depends on recognizing that cybersecurity buyers value trust and risk reduction more than feature depth or pricing alone. High-performing landing pages address security concerns immediately, display relevant certifications prominently, and present clear evidence of security outcomes so qualified prospects feel confident moving forward.
Frequently Asked Questions
What is CRO in cybersecurity?
Conversion rate optimization in cybersecurity focuses on turning security-conscious prospects who already completed extensive research into sales-qualified leads. Unlike general B2B SaaS CRO, cybersecurity optimization must address concerns about vendor trustworthiness, compliance capabilities, and security track records. The objective is reducing perceived risk through strategic trust signal placement and security-focused messaging.
What are strong CRO landing page examples for cybersecurity?
High-converting cybersecurity landing pages place security certifications above the fold, highlight specific security outcomes in testimonials, and cluster trust signals near conversion points. Effective examples include competitor comparison pages that address known security weaknesses, compliance-focused lead magnets, and hero sections that communicate security benefits instead of generic feature lists.
What are the most useful CRO tools for cybersecurity landing pages?
Essential tools for cybersecurity CRO include heatmap platforms that reveal visitor behavior, A/B testing tools for refining security messaging, and form analytics that reduce friction for privacy-conscious users. Security badge management systems, compliance documentation platforms, and testimonial collection tools designed for B2B security teams also support stronger conversion performance.
Where can I find 2026 cybersecurity landing page templates?
Effective cybersecurity landing page templates include dedicated sections for security certifications, compliance information, and specific security outcomes. The strongest templates feature trust-first hero sections, strategically placed customer logos from recognizable security-conscious companies, and forms tailored for privacy concerns. Templates should also reserve space for threat-specific messaging that addresses current cybersecurity challenges.
How do I measure cybersecurity landing page CRO success?
Success metrics for cybersecurity CRO extend beyond basic conversion rates and include lead quality indicators specific to security buyers. Track progression from landing page conversion to sales-qualified opportunities, since security prospects often require longer nurturing cycles. Monitor engagement with security-focused content, compliance documentation downloads, and movement through security-themed email sequences to understand the full impact of your optimization work.

