
Key Takeaways for Cybersecurity LTV-Focused Ads
- Cybersecurity SaaS needs 5:1 LTV:CAC ratios to offset high combined CAC of $35,000 to $55,000 and 18 to 24 month payback periods.
- LTV-focused ads prioritize revenue per customer over CPA and use intent-based ICP targeting with LinkedIn ABM for $100,000 to $300,000 ACV deals.
- Core pillars include AI LTV modeling with gradient boosting, trust-building creative, and multi-touch revenue attribution across 180 days or more.
- The 5-step playbook has delivered results such as $504,000 in net new ARR and 650% ROI on flat $1,250 per month retainers.
- Ready to achieve sustainable ARR growth? Audit your LTV:CAC performance with SaaSHero to uncover profitable growth opportunities.
Why LTV Matters More Than CPA in Cybersecurity SaaS
The cybersecurity buying journey involves multiple stakeholders, long evaluations, and strict compliance reviews, which makes traditional cost-per-acquisition metrics misleading. While FirstPageSage recommends B2B companies maintain at least a 3:1 LTV:CAC ratio, cybersecurity SaaS requires 5:1 LTV:CAC ratios to account for longer sales cycles and higher churn risks. The table below shows how much higher cybersecurity CAC is compared to general B2B SaaS while payback periods stay the same, which creates a profitability squeeze that only stronger LTV:CAC ratios can absorb.
| Metric | Cybersecurity SaaS | General B2B SaaS | Source |
|---|---|---|---|
| Average Combined CAC | $35,000–$55,000 | $702 | Culta.ai, Match-B2B |
| Inorganic CAC | ~$1,200 | ~$350 | FirstPageSage |
| Enterprise Payback Period | 18-24 months | 18-24 months | Match-B2B, knowledgelib.io |
The contrast between vanity metrics and revenue impact becomes clear when you look at pipeline quality. Low CPA campaigns generate high lead volume, but many of those leads lack budget, authority, or real intent and they drain sales resources without closing. This pattern occurs because CPA optimization rewards any conversion, not qualified buyers. LTV-focused campaigns accept higher initial costs and instead target high-intent CISOs with real purchasing power, which produces a smaller but far more valuable pipeline. Audit your current LTV:CAC performance with SaaSHero to identify which segments drive the most profitable growth.
What LTV-Focused Ads Mean for Cybersecurity Growth
LTV focused ads cybersecurity uses a strategic approach that prioritizes customer lifetime value instead of immediate conversion volume. This approach targets high-value prospects through intent-based cybersecurity ICP targeting and LinkedIn ABM campaigns that attract CISOs in finance, healthcare, and other regulated industries.
The main difference appears in the optimization goal. Traditional campaigns optimize for cost per lead, while LTV modeling cybersecurity ads optimize for revenue per customer acquired. This shift requires sophisticated attribution tracking that connects ad impressions to closed-won deals and supports budget allocation based on actual ARR contribution instead of vanity metrics. The table below highlights the four operational differences that separate LTV-focused campaigns from CPA-focused programs.
| Approach | CPA-Focused | LTV-Focused |
|---|---|---|
| Primary KPI | Cost Per Lead | Revenue Per Customer |
| Targeting Strategy | Broad Keywords | High-Intent ICP |
| Attribution Window | 30 Days | 180+ Days |
| Budget Allocation | Volume-Based | Revenue-Based |
Define your cybersecurity ICP targeting strategy with SaaSHero to move from volume-based campaigns to value-based growth.
Four Pillars of Cybersecurity LTV Ad Strategy
1. Cybersecurity ICP Targeting and LinkedIn ABM
Effective cybersecurity ICP targeting starts with analysis of your highest-value customers to identify shared firmographic and technographic traits. Reverse-enriching the top 50 closed-won accounts reveals patterns in time-to-close, expansion likelihood, and LTV that guide precise targeting parameters.
LinkedIn ABM cybersecurity campaigns should focus on specific job titles such as CISOs, IT Directors, and Compliance Officers within industries facing regulatory pressure or recent security incidents. LinkedIn-sourced deals are 28.6% larger in average contract value than Google-sourced deals, so this channel becomes essential for high-ACV cybersecurity sales.
2. AI-Driven LTV Modeling for Cybersecurity Ads
Advanced LTV modeling for cybersecurity ads uses machine learning algorithms such as Random Forests, Gradient Boosting, and Support Vector Machines to learn complex patterns and improve accuracy. These models combine demographic data, transactional history, and behavioral signals to predict customer value.
Gradient boosting models maintain accuracy over long periods and support precise budget allocation to high-value prospect segments. This capability allows cybersecurity companies to calculate maximum acceptable CAC for each customer tier and avoid overspending on low-value accounts.
3. Creative Strategy That Builds Trust With Risk-Averse Buyers
Cybersecurity buyers behave cautiously and respond best to creative that emphasizes trust, compliance, and risk reduction. Landing pages should feature security certifications, compliance badges, and case studies from similar organizations that faced comparable threats.
Heuristics-based CRO focuses on reducing friction while preserving credibility through social proof, clear value propositions, and transparent pricing information that addresses common cybersecurity procurement concerns.
4. Revenue Attribution and Tracking for Long Sales Cycles
Sophisticated revenue attribution connects ad impressions to closed-won revenue through CRM integration and multi-touch attribution models. Unlike last-click attribution that credits only the final touchpoint, multi-touch models distribute credit across all interactions in the buyer journey and reveal which channels contribute to high-value deals.
This approach enables optimization based on actual ARR contribution instead of lead volume. For example, a LinkedIn campaign that generates 10 leads per month can outperform a Google campaign that generates 100 leads if those 10 LinkedIn leads convert to $500,000 in ARR while the 100 Google leads produce only $200,000. Revenue attribution surfaces these patterns and supports the shift to LTV-focused campaign management. Schedule a technical consultation to implement multi-touch attribution for your cybersecurity funnel.
5-Step Implementation Playbook for High LTV Cybersecurity Leads
This five-step playbook turns the four pillars into a practical sequence you can execute. Each step builds on the previous one so your campaigns evolve from raw data to scalable ARR growth.
1. Audit Current LTV:CAC Performance: Analyze existing customer data to establish baseline LTV:CAC cybersecurity ratios and identify the highest-value customer segments. This audit shows which customer types generate the most revenue relative to acquisition cost and forms the foundation for every later targeting decision.
2. Build Cybersecurity ICP and ABM Lists: Use the high-value segments from your audit to create tiered ICP structures with Tier 1 for core prospects, Tier 2 for adjacent segments, and Tier 3 for experimental targeting based on firmographic, technographic, and behavioral attributes. These lists translate your audit insights into concrete targeting parameters for campaigns.
3. Launch Competitor Conquesting Campaigns: Activate search and social campaigns that target high-intent keywords such as “[competitor] pricing” and “[competitor] alternatives” with dedicated comparison landing pages. These pages highlight your unique value propositions and switching incentives, which capture buyers already in-market and considering alternatives.
4. Improve Conversion With Heuristics and CRO: Run systematic landing page experiments that focus on trust signals, clear value propositions, and friction reduction. This process increases conversion rates at each stage of the funnel without raising acquisition costs and prepares your account for efficient scaling.
5. Scale Based on ARR Signals: Use revenue attribution data to identify the highest-performing audience segments and creative combinations. Then shift and expand budget toward the combinations that generate the most net new ARR while pausing low-value segments.
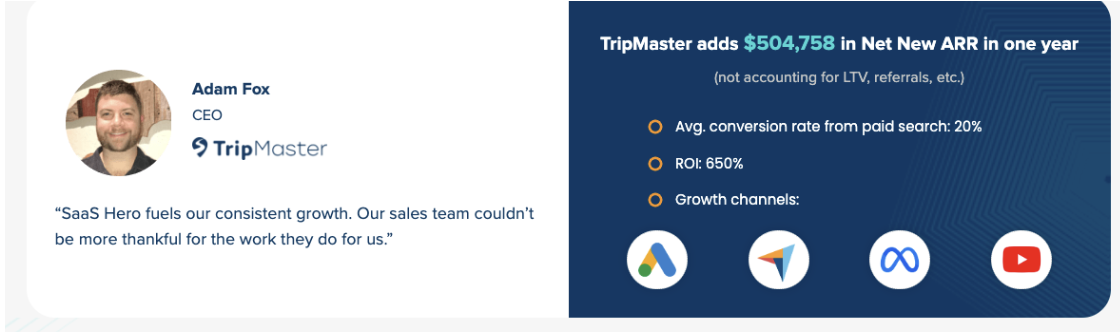
A transit software company (TripMaster) that followed this playbook achieved $504,758 in net new ARR within 12 months while maintaining efficient unit economics. Start a pilot program with SaaSHero to build a customized implementation roadmap based on your current metrics.
Risks, Benchmarks, and Proof From SaaSHero Campaigns
Common pitfalls include weak attribution tracking and percentage-of-spend agency models that reward higher budgets instead of performance. Benchmarks for 2026 show LinkedIn CPL ranging from $200 to $400 for B2B campaigns, while cost per SQL varies widely by vertical and deal size.
SaaSHero’s cybersecurity expertise includes delivering $504k net new ARR for clients at a 650% ROI while maintaining flat monthly retainers starting at $1,250. This month-to-month model removes the risk of long-term contracts and keeps agency incentives aligned with client revenue growth instead of ad spend volume.

The 650% ROI achieved through SaaSHero’s revenue-first approach shows how LTV-focused campaign management can outperform traditional volume-based agencies or in-house teams that lack specialized cybersecurity marketing experience.
FAQ
How to calculate LTV CAC ratio cybersecurity?
Calculate LTV:CAC by dividing customer lifetime value by customer acquisition cost. For cybersecurity SaaS, target ratios between 3:1 and 5:1, with higher ratios preferred because of longer sales cycles and compliance requirements. Include all acquisition costs such as ad spend, sales salaries, and marketing tools, and factor in gross margin when you calculate LTV so profitability estimates stay accurate.
What makes effective LinkedIn ABM cybersecurity campaigns?
Effective LinkedIn ABM cybersecurity campaigns target specific job titles within defined company segments that face security challenges or regulatory pressure. Build tiered audience lists based on company size, industry, and technology stack, then craft personalized messaging that addresses pain points such as compliance requirements, recent security incidents, or modernization initiatives.
What are the best LTV focused LinkedIn ads tips?
Focus on competitor conquesting campaigns that reach users researching alternative solutions, and use intent-based keywords that include pricing and comparison terms. Create dedicated landing pages for each competitor comparison, apply negative keywords to filter navigational searches, and optimize for revenue metrics instead of cost per lead to support sustainable growth.
How do cybersecurity campaign LTV strategies differ from other verticals?
Cybersecurity campaigns require longer attribution windows because of extended evaluations, a stronger emphasis on trust and compliance messaging, and targeting of risk-averse buyers who prioritize security over cost. AI modeling must account for regulatory triggers, security incidents, and compliance deadlines that drive purchasing decisions in cybersecurity markets.
What role does AI predictive modeling play in cybersecurity LTV optimization?
AI predictive modeling uses machine learning algorithms to analyze customer behavior patterns, predict lifetime value, and guide budget allocation across audience segments. Gradient boosting models maintain accuracy over long periods and support precise targeting of high-value prospects while reducing acquisition costs for lower-value segments.
Conclusion: Shift Cybersecurity Ads From CPA to LTV
The 2026 cybersecurity marketing landscape requires a shift from CPA-chasing to LTV-focused campaign management. This playbook provides the framework for achieving the 5:1 ratio discussed earlier through sophisticated ICP targeting, AI-powered modeling, and revenue-first attribution. Companies that adopt these strategies consistently outperform competitors that still optimize for vanity metrics.
Schedule a discovery call with SaaSHero to implement LTV focused ads cybersecurity strategies that drive sustainable ARR growth while preserving efficient unit economics.

